cdk-automated-waf
v1.0.5
Published
Cloudfront and ALB with Automated WAF
Downloads
63
Readme
cdk-automated-waf
This CDK Construct modify and rebuild from Cloudfront with Automated WAF.
The solution use CDK construct to automatically deploy a set of AWS WAF rules design to filter common web-based attacks.Users can select from preconfigured protective features that define the rules included in an AWS WAF web access control list (web ACL). After the solution deploys, AWS WAF begins inspecting web requests to the user’s existing Amazon CloudFront distributions、Application Load Balancers、API Gateway, and blocks them when applicable.
What is difference
The project is CDK Construct which is handy to integrate into your existing CDK project.
Support count mode for testing WAF rule, see API.md.
Support Application Load Balancers and API Gateway (The origin repository doesn't support ALB any more in next release, see issue )
AWS Shield Advance is optional (The origin repository enforce to enable it)
Construct Props
Ref API Reference
CloudFront Usage
const envUSEast1 = {
region: 'us-east-1',
account: process.env.CDK_DEFAULT_ACCOUNT,
};
new cdk.Stack(app, 'TestStackAutomatedWafForCloudFront', { env: envUSEast1 });
new AutomatedWaf(stackTest1, 'AutomatedWaf', {
waf2Scope: Waf2ScopeOption.CLOUDFRONT,
resourceNamingPrefix: 'CloudFront_ApiGW',
errorThreshold: 55,
requestThreshold: 300,
blockPeriod: 60,
logLevel: LogLevel.DEBUG,
});Notice the WAF region must be us-east-1 for CloudFront.
After deploying, it need to do two things on AWS Management Console.
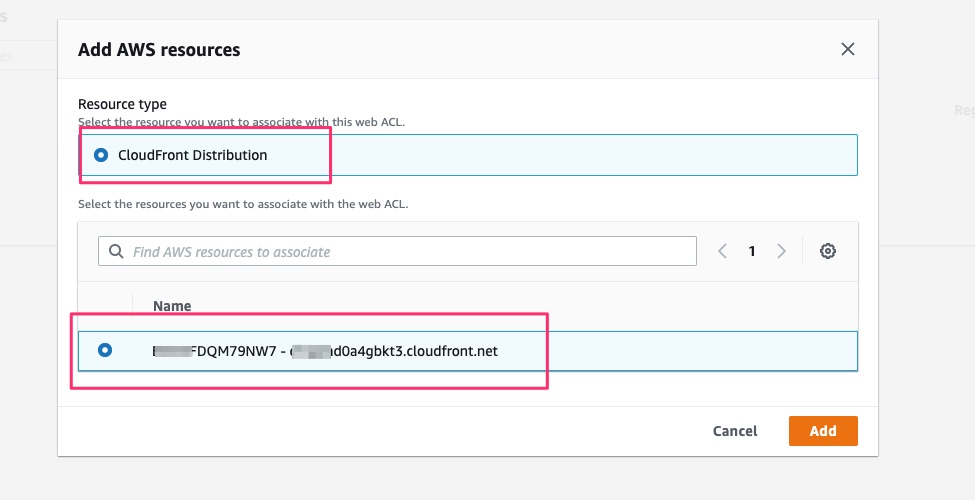
1. Attach Cloudfront to WAF.
Click add AWS Resources

Select existing CloudFront Distribution.
2. Set S3 bucket on CloudFront standand logging
Find S3 bucket name on CloudFormation output

Set CloudFront standard logging on CloudFront Settings
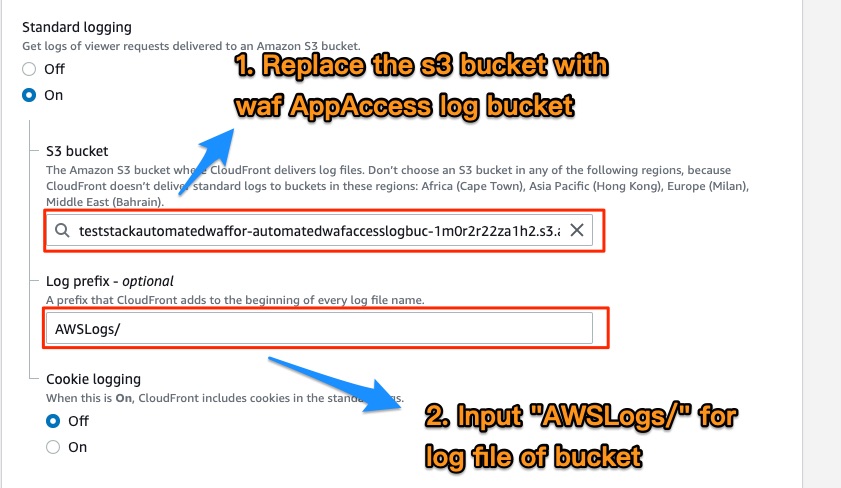
:warning: Log Prefix must be AWSLogs/
Application Load Balancers Usage
const env = {
region: process.env.CDK_DEFAULT_REGION,
account: process.env.CDK_DEFAULT_ACCOUNT,
};
new cdk.Stack(app, 'TestStackAutomatedWafForALB', { env });
const albArn = `arn:aws:elasticloadbalancing:${cdk.Aws.REGION}:${cdk.Aws.ACCOUNT_ID}:loadbalancer/app/ApiNe-Alb16-2VIC9075YQEZ/db92cdc88d2e7c9d`;
new AutomatedWaf(stackTest2, 'AutomatedWaf', {
waf2Scope: Waf2ScopeOption.REGIONAL,
associatedResourceArn: albArn,
resourceNamingPrefix: 'Alb_Api',
errorThreshold: 50,
requestThreshold: 300,
blockPeriod: 60,
logLevel: LogLevel.DEBUG,
});After deploying, follow these steps on AWS Management Console. See below:
Find S3 bucket name on CloudFormation output

Click Edit Attributes on Basic Configuration of Load Balancers
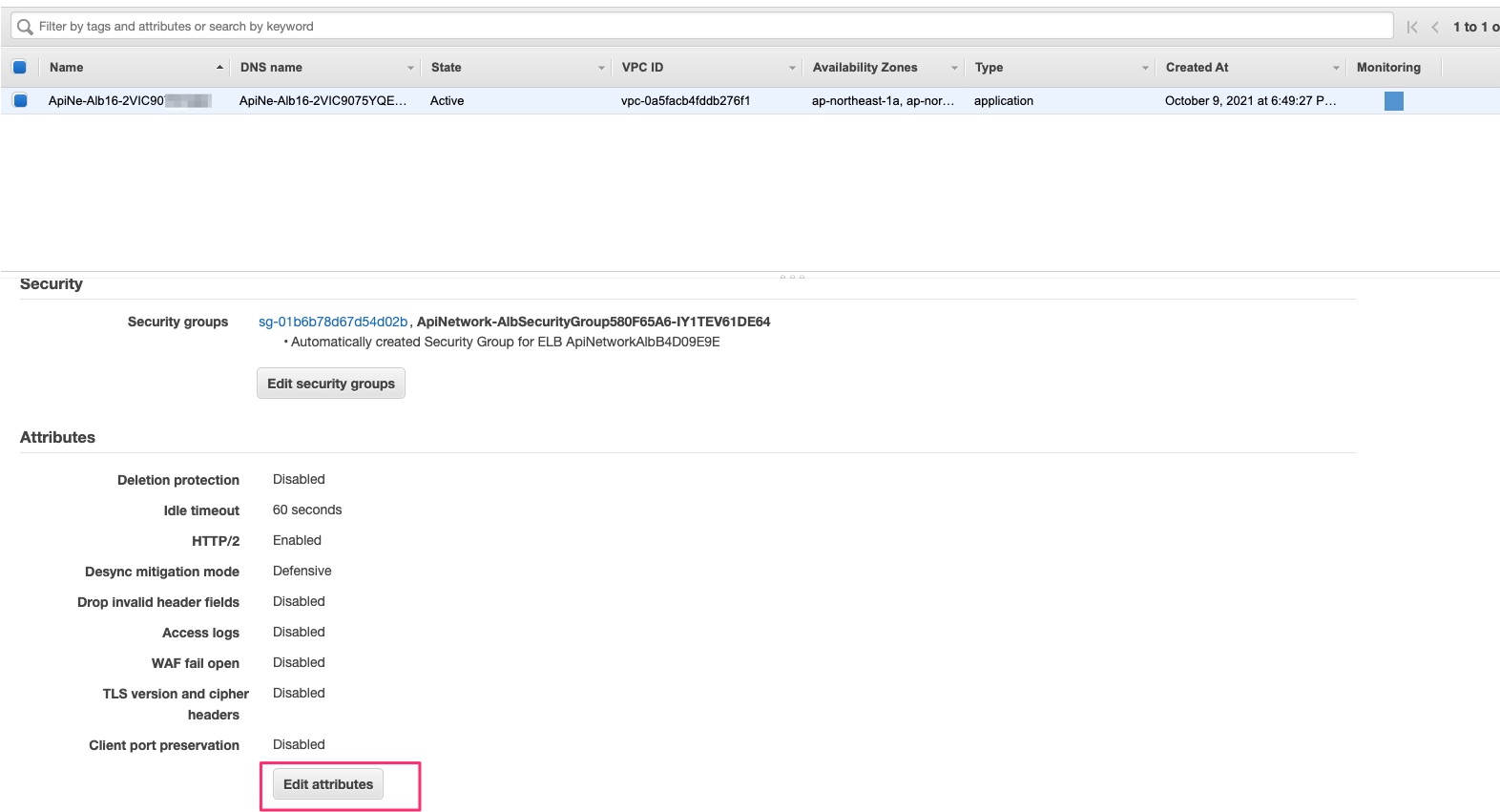
Enable Access logs and input S3 bucket

API Gateway Usage
const env = {
region: process.env.CDK_DEFAULT_REGION,
account: process.env.CDK_DEFAULT_ACCOUNT,
};
new cdk.Stack(app, 'TestStackAutomatedWafForApiGW', { env });
/**
* Ref Stage arn in https://docs.aws.amazon.com/apigateway/latest/developerguide/arn-format-reference.html
*/
const restApiArn = `arn:aws:apigateway:${cdk.Aws.REGION}::/restapis/0j90w09yf9/stages/prod`;
new AutomatedWaf(stackTest3, 'AutomatedWaf', {
waf2Scope: Waf2ScopeOption.REGIONAL,
associatedResourceArn: restApiArn,
resourceNamingPrefix: 'ApiGW',
errorThreshold: 50,
requestThreshold: 300,
blockPeriod: 60,
logLevel: LogLevel.DEBUG,
});Troubleshooting
If deployment error, the cloudFormation Error event like this
Received response status [FAILED] from custom resource. Message returned: 'HttpFloodLambdaLogParser' (RequestId: b4e08ea2-fe0a-46f8-98aa-6f96d4558579)If any custom resource deploy error like above, delete the stack and redeploy it that will pass.
