stringencrypt
v1.0.0
Published
Official JavaScript client for the StringEncrypt.com Web API — generate polymorphic decryptors for many programming languages.
Downloads
107
Maintainers
Readme
StringEncrypt — String & File Encryption for JavaScript Developers
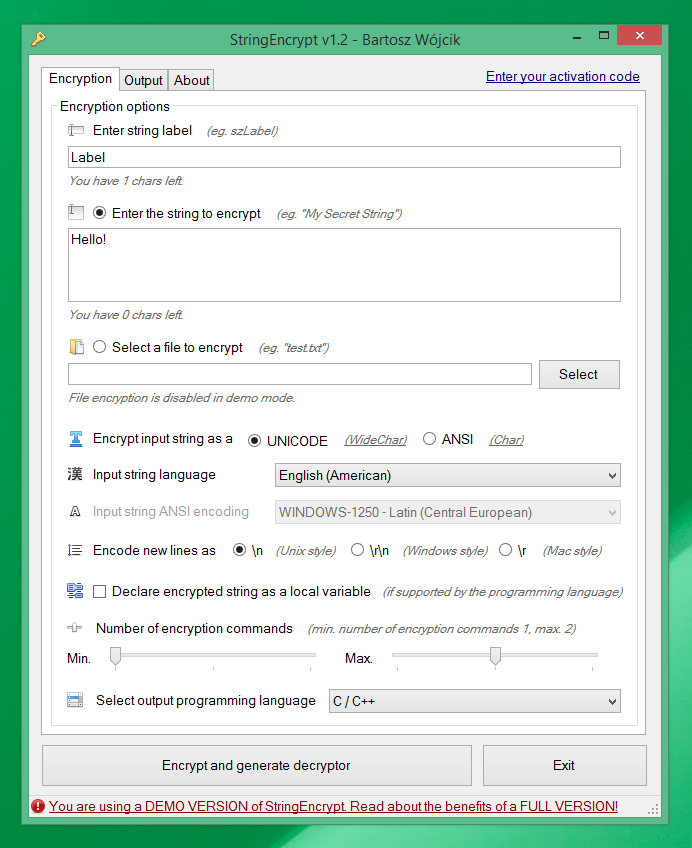
StringEncrypt allows you to encrypt strings and files using a randomly generated algorithm, generating a unique decryption code (so-called polymorphic code) each time in the selected programming language.
Available editions
StringEncrypt can be used:
- Directly on its website - https://www.stringencrypt.com/
- You can download standalone Windows client - https://www.stringencrypt.com/download/
- You can use it via WebAPI interface https://www.stringencrypt.com/api/
- Visual Studio Code extension - https://marketplace.visualstudio.com/items?itemName=PELock.stringencrypt
Plain text JavaScript string
var hiddenJavaScriptString = "How to encrypt strings in JavaScript? That\'s how!";Encrypted string in JavaScript (UNICODE) source code format
<script type="text/javascript">
// encrypted with https://www.stringencrypt.com (v1.5.0) [JavaScript]
// hiddenJavaScriptString = "How to encrypt strings in JavaScript? That\'s how!"
var hiddenJavaScriptString = "\u98EC\u8931\u84BF\u08CA\uA678\u97CB\uBD14\u3A9B" +
"\u3BD4\uD21D\uAA4B\u9A60\u9A11\uBF64\u99DB\u549D" +
"\u5BD7\u034C\uD869\uA2A6\uAA7F\u97AF\u7D26\uBEFD" +
"\u4865\u1981\u9F3A\u9254\u36C7\u3F07\uD9A5\uA14C" +
"\u50E2\uF715\u1CA3\uE7DF\u18B2\uCEC8\uB697\u5BCE" +
"\u55F5\uB391\u232E\u82D0\u12BD\uB78E\uB1E9\uBF57" +
"\uF0FB";
for (var rAQLB = 0, JyFfr = 0; rAQLB < 49; rAQLB++)
{
JyFfr = hiddenJavaScriptString.charCodeAt(rAQLB);
JyFfr = (JyFfr ^ (((JyFfr & 0xFFFF) << 15) & 0xFFFF)) & 0xFFFF;
JyFfr = ((JyFfr & 0xFFFF) + rAQLB) & 0xFFFF;
for (var ZvqmG = 0; ZvqmG < 2; ZvqmG++)
{
JyFfr = (JyFfr ^ 0x702B) & 0xFFFF;
for (var VbsGy = 0; VbsGy < 3; VbsGy++)
{
for (var ToslH = 0; ToslH < 4; ToslH++)
{
JyFfr = (((JyFfr & 0xFFFF) << 8) | ((JyFfr & 0xFFFF) >>> 8)) & 0xFFFF;
JyFfr = (((JyFfr & 0xFFFF) >>> (rAQLB % 16)) | ((JyFfr & 0xFFFF) << (16 - (rAQLB % 16)))) & 0xFFFF;
}
for (var oreEi = 0; oreEi < 3; oreEi++)
{
JyFfr = ((JyFfr & 0xFFFF) - 0x804C) & 0xFFFF;
JyFfr = (((~(JyFfr & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
JyFfr = ((JyFfr & 0xFFFF) - 0xDECB) & 0xFFFF;
}
JyFfr = ((JyFfr & 0xFFFF) + 0xF170) & 0xFFFF;
}
for (var viVTW = 0; viVTW < 2; viVTW++)
{
for (var eUMlC = 0; eUMlC < 2; eUMlC++)
{
JyFfr = (JyFfr ^ rAQLB) & 0xFFFF;
}
for (var bZrxF = 0; bZrxF < 3; bZrxF++)
{
JyFfr = (((JyFfr & 0xFFFF) << (rAQLB % 16)) | ((JyFfr & 0xFFFF) >>> (16 - (rAQLB % 16)))) & 0xFFFF;
JyFfr = (JyFfr ^ (((JyFfr & 0xFFFF) << 11) & 0xFFFF)) & 0xFFFF;
}
JyFfr = (((JyFfr & 0xFFFF) << 9) | ((JyFfr & 0xFFFF) >>> 7)) & 0xFFFF;
}
}
JyFfr = (((JyFfr & 0xFFFF) >>> 8) | ((JyFfr & 0xFFFF) << 8)) & 0xFFFF;
JyFfr = (((JyFfr & 0xFFFF) << 1) | ((JyFfr & 0xFFFF) >>> 15)) & 0xFFFF;
for (var nzOko = 0; nzOko < 4; nzOko++)
{
JyFfr = (((JyFfr & 0xFFFF) >>> (rAQLB % 16)) | ((JyFfr & 0xFFFF) << (16 - (rAQLB % 16)))) & 0xFFFF;
}
JyFfr = (JyFfr ^ 0xFFFF) & 0xFFFF;
JyFfr = (((JyFfr & 0xFFFF) << (rAQLB % 16)) | ((JyFfr & 0xFFFF) >>> (16 - (rAQLB % 16)))) & 0xFFFF;
JyFfr = ((JyFfr & 0xFFFF) + 0xCB9C) & 0xFFFF;
JyFfr = ((JyFfr & 0xFFFF) - rAQLB) & 0xFFFF;
for (var xiFsy = 0; xiFsy < 3; xiFsy++)
{
for (var JPxQM = 0; JPxQM < 3; JPxQM++)
{
JyFfr = (((JyFfr & 0xFFFF) << 10) | ((JyFfr & 0xFFFF) >>> 6)) & 0xFFFF;
}
}
JyFfr = ((JyFfr & 0xFFFF) + rAQLB) & 0xFFFF;
for (var DBPwg = 0; DBPwg < 4; DBPwg++)
{
JyFfr = (((JyFfr & 0xFFFF) << 14) | ((JyFfr & 0xFFFF) >>> 2)) & 0xFFFF;
}
hiddenJavaScriptString = hiddenJavaScriptString.substr(0, rAQLB) + String.fromCharCode(JyFfr & 0xFFFF) + hiddenJavaScriptString.substr(rAQLB + 1);
}
alert(hiddenJavaScriptString);
</script>The problem with plain text strings
I'm a developer, and I love programming. I'm also an avid reverse engineer. I perform a wide array of software analysis in my daily work and sometimes I find things in compiled applications that shouldn't be exposed to the first person with a simple hex-editor in hand.
What can be found in application binaries?
Everything! I've listed a few examples of the things I found below. Sometimes these things shouldn't even be included in applications at all (they are there due to poor design choices or rushed work), but some are just cannot be avoided.
- API keys
- Database passwords
- FTP passwords
- Login credentials
- Encryption & decryption keys
- Custom code scripts in readable text
- Complex SQL queries in plain text
- Hidden website endpoints
- BitCoin wallets locations
- ...and many more
Ask yourself, did you ever put some sensitive content in your software that you later regret?
Why should I care?
If any of these things were to fall into the wrong hands, they could be used to compromise your software or your infrastructure.
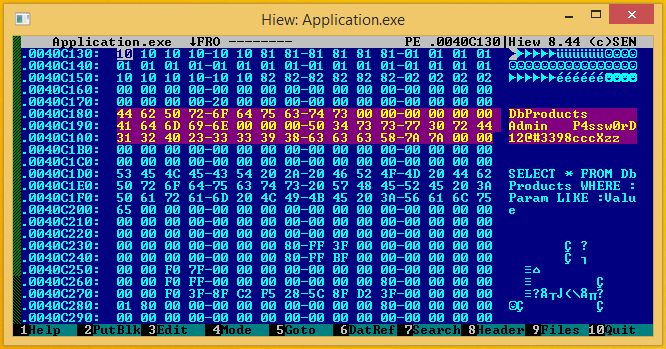
Take for example database passwords. A competitor could use them to view your database structure or dump all of its contents. You don't want to lose all your hard work because someone with a simple hex-editor can discover your password in plain text.
The solution — String Encrypt
I've decided to create a simple service called String Encrypt for developers, offering fast string & file encryption without the need to write custom encryption tools over and over again because I did that many times.
String Encrypt can help you hide the things that shouldn't be visible at first glance to anyone with a hex-editor.
Say hello to polymorphic encryption!
Forget about simple xor encryption! StringEncrypt comes with a unique encryption engine.
It's a polymorphic encryption engine, similar to the encryption methods used by the software protection solutions and advanced computer viruses.
How it works?
Let me explain how the polymorphic encryption process works.
- A random set of encryption commands is selected (
xor,addition,subtraction,bit rotations,bit shifts,logical negationetc.). - A random set of helper
encryption keysis generated. - Every byte of the input string is encrypted with every encryption command in the random set.
- Nested encryption loops are constructed
- The decryption code in the selected programming language is generated with a reverse set of encryption commands.
You can learn more about polymorphic engines from my articles and projects:
- How to build a polymorphic engine in C++ - https://www.pelock.com/articles/polymorphic-encryption-algorithms
- Polymorphic engine in 32-bit MASM assembler - https://github.com/PELock/Simple-Polymorphic-Engine-SPE32
- Poly Polymorphic Engine - https://www.pelock.com/products/poly-polymorphic-engine
What does it mean?
The encrypted content is different every time you apply StringEncrypt encryption to it.
The algorithm is always unique, the encryption keys are always randomly selected and the decryption code is also unique for every time you use our encryption.
StringEncrypt features
- Out of box support for
UNICODE(WideChar type inC/C++languages),UTF-8(multibyte) &ANSI(single byte) strings encodings - Configurable minimum & maximum number of encryption commands
- Different ways to store the encrypted string (as a
globalorlocalvariable if the selected programming language supports it) - Wide array of supported programming languages
- You can automate the encryption process in your builds using our
WebAPIinterface (JavaScript,PHP, andPythonbindings)
How to use StringEncrypt from Node.js code?
The preferred way to install the StringEncrypt module is via npm.
Run:
npm install stringencryptThe package is published at https://www.npmjs.com/package/stringencrypt
Basic string encryption usage example (with default options)
///////////////////////////////////////////////////////////////////////////////
//
// StringEncrypt WebApi interface usage example.
//
// In this example we will encrypt sample string with default options.
//
// Version : v1.0.0
// Language : JavaScript
// Author : Bartosz Wójcik
// Project page : https://www.stringencrypt.com
// Web page : https://www.pelock.com
//
///////////////////////////////////////////////////////////////////////////////
import { ErrorCode, StringEncrypt } from 'stringencrypt';
const stringEncrypt = new StringEncrypt('YOUR-API-KEY-HERE'); // leave empty for demo mode
const result = await stringEncrypt.encryptString('Hello!', '$label');
if (result === false) {
console.log('Cannot connect to the API.');
process.exit(1);
}
if (result.error !== ErrorCode.SUCCESS) {
console.log(`API error: ${String(result.error ?? 'unknown')}`);
process.exit(1);
}
console.log(String(result.source) + '\n');Return values:
result["error"] (number)- error coderesult["source"] (string)- decryptor source coderesult["expired"] (boolean)- expiration flagresult["credits_left"] (number)- number of credits leftresult["credits_total"] (number)- initial number of credits
Error codes:
ERROR_SUCCESS (0)- everything went fineERROR_EMPTY_LABEL (1)- label parameter is emptyERROR_LENGTH_LABEL (2)- label length is too longERROR_EMPTY_STRING (3)- input string is emptyERROR_EMPTY_BYTES (4)- input file bytes array is emptyERROR_EMPTY_INPUT (5)- input source (either string or file) is missingERROR_LENGTH_STRING (6)- string length is too longERROR_INVALID_LANG (7)- programming language not supportedERROR_INVALID_LOCALE (8)- language locale is not supportedERROR_CMD_MIN (9)- invalid number of minimum encryption commandsERROR_CMD_MAX (10)- invalid number of maximum encryption commandsERROR_LENGTH_BYTES (11)- bytes/file length is too longERROR_DEMO (100)- you need a valid code to use full version features
Custom string encryption for other programming languages
///////////////////////////////////////////////////////////////////////////////
//
// StringEncrypt WebApi interface usage example.
//
// In this example we will encrypt sample string with default options.
//
// Version : v1.0.0
// Language : JavaScript
// Author : Bartosz Wójcik
// Project page : https://www.stringencrypt.com
// Web page : https://www.pelock.com
//
///////////////////////////////////////////////////////////////////////////////
import { ErrorCode, Language, NewLine, StringEncrypt } from 'stringencrypt';
const stringEncrypt = new StringEncrypt('YOUR-API-KEY-HERE'); // leave empty for demo mode
stringEncrypt
.setCompression(false)
.setUnicode(true)
.setLangLocale('en_US.utf8')
.setNewLines(NewLine.Lf)
.setLanguage(Language.Cpp)
.setCmdMin(1)
.setCmdMax(3)
.setLocal(false);
const result = await stringEncrypt.encryptString('Hello!', 'wszLabel');
if (result === false) {
console.log('Cannot connect to the API.');
process.exit(1);
}
if (result.error !== ErrorCode.SUCCESS) {
console.log(`API error: ${String(result.error ?? 'unknown')}`);
process.exit(1);
}
console.log(String(result.source) + '\n');Return values:
result["error"] (number)- error coderesult["source"] (string)- decryptor source coderesult["expired"] (boolean)- expiration flagresult["credits_left"] (number)- number of credits leftresult["credits_total"] (number)- initial number of credits
Error codes:
ERROR_SUCCESS (0)- everything went fineERROR_EMPTY_LABEL (1)- label parameter is emptyERROR_LENGTH_LABEL (2)- label length is too longERROR_EMPTY_STRING (3)- input string is emptyERROR_EMPTY_BYTES (4)- input file bytes array is emptyERROR_EMPTY_INPUT (5)- input source (either string or file) is missingERROR_LENGTH_STRING (6)- string length is too longERROR_INVALID_LANG (7)- programming language not supportedERROR_INVALID_LOCALE (8)- language locale is not supportedERROR_CMD_MIN (9)- invalid number of minimum encryption commandsERROR_CMD_MAX (10)- invalid number of maximum encryption commandsERROR_LENGTH_BYTES (11)- bytes/file length is too longERROR_DEMO (100)- you need a valid code to use full version features
Encrypt binary file content
///////////////////////////////////////////////////////////////////////////////
//
// StringEncrypt WebApi interface usage example.
//
// In this example we will encrypt sample file with default options.
//
// Version : v1.0.0
// Language : JavaScript
// Author : Bartosz Wójcik
// Project page : https://www.stringencrypt.com
// Web page : https://www.pelock.com
//
///////////////////////////////////////////////////////////////////////////////
import { dirname, join } from 'node:path';
import { fileURLToPath } from 'node:url';
import { ErrorCode, Language, NewLine, StringEncrypt } from 'stringencrypt';
const __dirname = dirname(fileURLToPath(import.meta.url));
const stringEncrypt = new StringEncrypt('YOUR-API-KEY-HERE'); // leave empty for demo mode
stringEncrypt
.setCompression(false)
.setUnicode(true)
.setLangLocale('en_US.utf8')
.setNewLines(NewLine.Lf)
.setAnsiEncoding('WINDOWS-1250')
.setLanguage(Language.Php)
.setCmdMin(1)
.setCmdMax(3)
.setLocal(false);
// Full license: raw bytes from file (demo may return ERROR_DEMO).
const result = await stringEncrypt.encryptFileContents(join(__dirname, 'sample.bin'), '$label');
if (result === false) {
console.log('Cannot connect to the API or file is missing/empty.');
process.exit(1);
}
if (result.error !== ErrorCode.SUCCESS) {
console.log(`API error: ${String(result.error ?? 'unknown')}`);
process.exit(1);
}
console.log(String(result.source) + '\n');Return values:
result["error"] (number)- error coderesult["source"] (string)- decryptor source coderesult["expired"] (boolean)- expiration flagresult["credits_left"] (number)- number of credits leftresult["credits_total"] (number)- initial number of credits
Error codes:
ERROR_SUCCESS (0)- everything went fineERROR_EMPTY_LABEL (1)- label parameter is emptyERROR_LENGTH_LABEL (2)- label length is too longERROR_EMPTY_STRING (3)- input string is emptyERROR_EMPTY_BYTES (4)- input file bytes array is emptyERROR_EMPTY_INPUT (5)- input source (either string or file) is missingERROR_LENGTH_STRING (6)- string length is too longERROR_INVALID_LANG (7)- programming language not supportedERROR_INVALID_LOCALE (8)- language locale is not supportedERROR_CMD_MIN (9)- invalid number of minimum encryption commandsERROR_CMD_MAX (10)- invalid number of maximum encryption commandsERROR_LENGTH_BYTES (11)- bytes/file length is too longERROR_DEMO (100)- you need a valid code to use full version features
Check the status of the activation code and show current limitations
This example shows how to get information about the current activation code and its features.
///////////////////////////////////////////////////////////////////////////////
//
// StringEncrypt WebApi interface usage example.
//
// In this example we will verify our activation code status.
//
// Version : v1.0.0
// Language : JavaScript
// Author : Bartosz Wójcik
// Project page : https://www.stringencrypt.com
// Web page : https://www.pelock.com
//
///////////////////////////////////////////////////////////////////////////////
import { StringEncrypt } from 'stringencrypt';
const stringEncrypt = new StringEncrypt('');
const result = await stringEncrypt.isDemo();
if (result === false) {
console.log('Cannot connect to the API.');
process.exit(1);
}
if (result.demo) {
console.log('DEMO mode');
} else {
console.log('FULL mode');
console.log(`Credits left: ${String(result.credits_left ?? '')}`);
}
console.log(`Label max length: ${String(result.label_limit ?? '')}`);
console.log(`String max length: ${String(result.string_limit ?? '')}`);
console.log(`Bytes max length: ${String(result.bytes_limit ?? '')}`);
console.log(`cmd_min / cmd_max: ${String(result.cmd_min ?? '')} / ${String(result.cmd_max ?? '')}`);Return values:
result["demo"] (boolean)- demo mode flagresult["label_limit"] (number)- label limit lengthresult["string_limit"] (number)- string/file limit lengthresult["credits_left"] (number)- number of credits leftresult["credits_total"] (number)- initial number of creditsresult["cmd_min"] (number)- minimum number of encryption commandsresult["cmd_max"] (number)- maximum number of encryption commands
Supported programming languages
StringEncrypt engine supports code generation for the following programming languages:
- C & C++
- C# (C Sharp for .NET)
- Visual Basic .NET (VB.NET)
- Delphi / Pascal
- Java
- Kotlin
- JavaScript
- Python
- PHP
- Ruby
- Dart
- Go
- Rust
- Swift
- Lua
- Objective-C
- AutoIt
- PowerShell
- Haskell
- MASM assembler
- FASM assembler
- NASM assembler
Some examples of generated source code for supported programming languages (with display / run example enabled, matching the full client include example option):
C/C++ encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [C/C++]
#include <cstdio>
#include <cwchar>
// wszLabel = "C/C++ String Encryption"
wchar_t wszLabel[24];
wszLabel[20] = 0xEDD6; wszLabel[22] = 0xA64D; wszLabel[3] = 0x733C; wszLabel[19] = 0x96B6;
wszLabel[12] = 0xBCA7; wszLabel[6] = 0xDBD5; wszLabel[18] = 0x8D05; wszLabel[1] = 0xD61B;
wszLabel[9] = 0x16AC; wszLabel[13] = 0xCA4A; wszLabel[16] = 0xAB02; wszLabel[8] = 0xB392;
wszLabel[21] = 0xE785; wszLabel[10] = 0x18AB; wszLabel[14] = 0x2AF8; wszLabel[23] = 0x7099;
wszLabel[5] = 0xAF1B; wszLabel[15] = 0xFC72; wszLabel[7] = 0x05AE; wszLabel[0] = 0x9BF3;
wszLabel[2] = 0x14D8; wszLabel[4] = 0xD30F; wszLabel[11] = 0xEDE7; wszLabel[17] = 0x1158;
for (volatile unsigned int iZASt = 0, tmLMB = 0; iZASt < 24; iZASt++)
{
tmLMB = wszLabel[iZASt];
for (unsigned int sfIcm = 0; sfIcm < 2; sfIcm++)
{
for (unsigned int MUhVa = 0; MUhVa < 3; MUhVa++)
{
tmLMB = (tmLMB ^ (((tmLMB & 0xFFFF) << 15) & 0xFFFF)) & 0xFFFF;
tmLMB = (((tmLMB & 0xFFFF) << (iZASt % 16)) | ((tmLMB & 0xFFFF) >> (16 - (iZASt % 16)))) & 0xFFFF;
}
}
tmLMB = (tmLMB ^ 0x2BFD) & 0xFFFF;
tmLMB = (((tmLMB & 0xFFFF) >> 8) | ((tmLMB & 0xFFFF) << 8)) & 0xFFFF;
for (unsigned int qiTBF = 0; qiTBF < 2; qiTBF++)
{
tmLMB = ((tmLMB & 0xFFFF) - iZASt) & 0xFFFF;
tmLMB = (((tmLMB & 0xFFFF) >> 8) | ((tmLMB & 0xFFFF) << 8)) & 0xFFFF;
}
tmLMB = ((tmLMB & 0xFFFF) - 0x51B1) & 0xFFFF;
tmLMB = (((tmLMB & 0xFFFF) >> 8) | ((tmLMB & 0xFFFF) << 8)) & 0xFFFF;
tmLMB = ((tmLMB ^ 0xFFFF) & 0xFFFF);
tmLMB = ((tmLMB & 0xFFFF) + iZASt) & 0xFFFF;
for (unsigned int HOCjn = 0; HOCjn < 4; HOCjn++)
{
tmLMB = (((tmLMB & 0xFFFF) >> 8) | ((tmLMB & 0xFFFF) << 8)) & 0xFFFF;
tmLMB = ((tmLMB & 0xFFFF) - iZASt) & 0xFFFF;
for (unsigned int JpQxh = 0; JpQxh < 2; JpQxh++)
{
tmLMB = (((tmLMB & 0xFFFF) >> 12) | ((tmLMB & 0xFFFF) << 4)) & 0xFFFF;
}
}
wszLabel[iZASt] = tmLMB;
}
fputws(wszLabel, stdout);
fputwc(L'\n', stdout);C# Sharp encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [C#]
// superSecretString = "Easy encryption in C#"
String superSecretString = "\uA1A2\uE379\uB64C\u7816\u238A\uD7E4\u0CFA\uD465" +
"\u7CE4\uA305\u2C46\uD27B\u533A\u6F43\u91A5\u3B36" +
"\u181E\uC1B8\uA827\uC1FC\u9073";
for (int ugcqt = 0, TSGdn = 0; ugcqt < 21; ugcqt++)
{
TSGdn = superSecretString[ugcqt];
TSGdn = (((TSGdn & 0xFFFF) << (ugcqt % 16)) | ((TSGdn & 0xFFFF) >> (16 - (ugcqt % 16)))) & 0xFFFF;
TSGdn = (TSGdn ^ ugcqt) & 0xFFFF;
for (int IjFDX = 0; IjFDX < 3; IjFDX++)
{
for (int scVKQ = 0; scVKQ < 2; scVKQ++)
{
TSGdn = (TSGdn ^ (((TSGdn & 0xFFFF) << 9) & 0xFFFF)) & 0xFFFF;
for (int tKeJi = 0; tKeJi < 4; tKeJi++)
{
TSGdn = (((TSGdn & 0xFFFF) << (ugcqt % 16)) | ((TSGdn & 0xFFFF) >> (16 - (ugcqt % 16)))) & 0xFFFF;
TSGdn = ((TSGdn & 0xFFFF) - 0x7198) & 0xFFFF;
TSGdn = (TSGdn ^ 0xFFFF) & 0xFFFF;
}
TSGdn = (((TSGdn & 0xFFFF) << 6) | ((TSGdn & 0xFFFF) >> 10)) & 0xFFFF;
}
TSGdn = ((TSGdn & 0xFFFF) + 1) & 0xFFFF;
for (int Hmtef = 0; Hmtef < 3; Hmtef++)
{
for (int CEwoz = 0; CEwoz < 2; CEwoz++)
{
TSGdn = (TSGdn ^ (((TSGdn & 0xFFFF) << 11) & 0xFFFF)) & 0xFFFF;
}
}
}
for (int OomDf = 0; OomDf < 3; OomDf++)
{
for (int WCOqH = 0; WCOqH < 4; WCOqH++)
{
TSGdn = (((TSGdn & 0xFFFF) >> 1) | ((TSGdn & 0xFFFF) << 15)) & 0xFFFF;
}
for (int ikutC = 0; ikutC < 2; ikutC++)
{
for (int HJjpq = 0; HJjpq < 2; HJjpq++)
{
TSGdn = (TSGdn ^ 0x5539) & 0xFFFF;
}
for (int FKCPT = 0; FKCPT < 3; FKCPT++)
{
TSGdn = (TSGdn ^ 0xFFFF) & 0xFFFF;
TSGdn = ((TSGdn & 0xFFFF) + 0xC1C1) & 0xFFFF;
}
TSGdn = (TSGdn ^ (((TSGdn & 0xFFFF) << 10) & 0xFFFF)) & 0xFFFF;
}
}
TSGdn = ((TSGdn & 0xFFFF) - ugcqt) & 0xFFFF;
TSGdn = ((TSGdn & 0xFFFF) + 1) & 0xFFFF;
TSGdn = ((TSGdn & 0xFFFF) + 0x6B27) & 0xFFFF;
for (int knhQm = 0; knhQm < 2; knhQm++)
{
for (int dxIem = 0; dxIem < 4; dxIem++)
{
for (int LvAum = 0; LvAum < 3; LvAum++)
{
TSGdn = (((TSGdn & 0xFFFF) >> 2) | ((TSGdn & 0xFFFF) << 14)) & 0xFFFF;
TSGdn = (((~(TSGdn & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
TSGdn = (((TSGdn & 0xFFFF) << (ugcqt % 16)) | ((TSGdn & 0xFFFF) >> (16 - (ugcqt % 16)))) & 0xFFFF;
}
}
TSGdn = ((TSGdn & 0xFFFF) - 1) & 0xFFFF;
TSGdn = (TSGdn ^ ugcqt) & 0xFFFF;
}
TSGdn = (TSGdn ^ 0xEDF3) & 0xFFFF;
TSGdn = (((TSGdn & 0xFFFF) >> (ugcqt % 16)) | ((TSGdn & 0xFFFF) << (16 - (ugcqt % 16)))) & 0xFFFF;
TSGdn = (((~(TSGdn & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
for (int tJDYH = 0; tJDYH < 2; tJDYH++)
{
for (int jqFXP = 0; jqFXP < 4; jqFXP++)
{
TSGdn = (((TSGdn & 0xFFFF) >> (ugcqt % 16)) | ((TSGdn & 0xFFFF) << (16 - (ugcqt % 16)))) & 0xFFFF;
TSGdn = (((TSGdn & 0xFFFF) << 3) | ((TSGdn & 0xFFFF) >> 13)) & 0xFFFF;
TSGdn = ((TSGdn & 0xFFFF) - 0x4E43) & 0xFFFF;
}
}
superSecretString = superSecretString.Substring(0, ugcqt) + (char)(TSGdn & 0xFFFF) + superSecretString.Substring(ugcqt + 1);
}
MessageBox.Show(superSecretString);Visual Basic .NET encryption (UNICODE example)
' encrypted with https://www.stringencrypt.com (v1.5.0) [Visual Basic .NET]
' vbSecret = "Option Strict On in VB.NET"
Dim HudbE() As Integer = { &H6606, &H39FF, &H14BC, &HFFD1, &HF714, &HF242, &H6EBC, &H2E90,
&H2E4B, &H8DF2, &H9DD0, &H85C4, &HC1C3, &H37DD, &HD0D9, &H1C50,
&H3716, &H372F, &H13AC, &HF731, &HF5EC, &HF172, &H6F64, &H2F1B,
&HEE8D, &HAE75 }
Dim vbSecret As String
Dim XidVf As Integer
Dim oqtRy As Integer
Dim SKjiG As Integer
Dim QhyUd As Integer
Dim YHFWS As Integer
Dim EVNCa As Integer
Dim eRLNZ As Integer
For eRLNZ = 0 To 25
XidVf = HudbE(eRLNZ)
XidVf = (XidVf Xor eRLNZ) And &HFFFF
XidVf = ((XidVf And &HFFFF) + 1) And &HFFFF
For oqtRy = 0 To 1
For SKjiG = 0 To 3
XidVf = ((XidVf And &HFFFF) - eRLNZ) And &HFFFF
Next
XidVf = ((XidVf And &HFFFF) - &HF6B4) And &HFFFF
Next
XidVf = ((XidVf And &HFFFF) + 1) And &HFFFF
XidVf = (((XidVf And &HFFFF) << (eRLNZ Mod 16)) Or ((XidVf And &HFFFF) >> (16 - (eRLNZ Mod 16)))) And &HFFFF
For QhyUd = 0 To 3
For YHFWS = 0 To 2
XidVf = ((XidVf And &HFFFF) - 1) And &HFFFF
Next
XidVf = ((XidVf And &HFFFF) - &H4A45) And &HFFFF
XidVf = (XidVf Xor eRLNZ) And &HFFFF
Next
XidVf = (((XidVf And &HFFFF) >> 8) Or ((XidVf And &HFFFF) << 8)) And &HFFFF
XidVf = (XidVf Xor (((XidVf And &HFFFF) << 15) And &HFFFF)) And &HFFFF
For EVNCa = 0 To 3
XidVf = (XidVf Xor eRLNZ) And &HFFFF
XidVf = (((XidVf And &HFFFF) >> 8) Or ((XidVf And &HFFFF) << 8)) And &HFFFF
Next
vbSecret = vbSecret + ChrW(XidVf And &HFFFF)
Next eRLNZ
MessageBox.Show(vbSecret)Delphi & Pascal encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Delphi / Pascal]
var
// mySecret = "Delphi is awesome!"
mySecret: array[0..19] of WideChar;
HFisk: Integer;
ZnzLM: Integer;
XMlUh: Integer;
pSdQr: Integer;
clrza: Integer;
GPvNR: Integer;
lFOKB: Integer;
begin
mySecret[6] := WideChar($EF77); mySecret[15] := WideChar($766A);
mySecret[5] := WideChar($4E77); mySecret[1] := WideChar($F277);
mySecret[2] := WideChar($3B77); mySecret[17] := WideChar($FE72);
mySecret[14] := WideChar($7268); mySecret[9] := WideChar($9362);
mySecret[0] := WideChar($EB77); mySecret[3] := WideChar($4B77);
mySecret[13] := WideChar($E06A); mySecret[16] := WideChar($0A75);
mySecret[11] := WideChar($5462); mySecret[4] := WideChar($AF74);
mySecret[7] := WideChar($2A77); mySecret[10] := WideChar($F060);
mySecret[8] := WideChar($FA64); mySecret[18] := WideChar($5F70);
mySecret[12] := WideChar($4464);
for lFOKB := 0 to 19 do
begin
HFisk := Ord(mySecret[lFOKB]);
HFisk := (HFisk xor $FFFF) and $FFFF;
HFisk := (HFisk xor lFOKB) and $FFFF;
HFisk := ((HFisk and $FFFF) - $0124) and $FFFF;
HFisk := ((HFisk and $FFFF) - lFOKB) and $FFFF;
HFisk := (((HFisk and $FFFF) shr 8) or ((HFisk and $FFFF) shl 8)) and $FFFF;
HFisk := (HFisk xor $168C) and $FFFF;
HFisk := (((HFisk and $FFFF) shr 8) or ((HFisk and $FFFF) shl 8)) and $FFFF;
HFisk := (((HFisk and $FFFF) xor $FFFF) + 1) and $FFFF;
HFisk := (((HFisk and $FFFF) shr 8) or ((HFisk and $FFFF) shl 8)) and $FFFF;
HFisk := (HFisk xor $FFFF) and $FFFF;
for ZnzLM := 0 to 3 do
begin
HFisk := ((HFisk and $FFFF) + lFOKB) and $FFFF;
for XMlUh := 0 to 2 do
begin
HFisk := (HFisk xor lFOKB) and $FFFF;
HFisk := ((HFisk and $FFFF) + lFOKB) and $FFFF;
HFisk := (HFisk xor ((HFisk and $FFFF) shr 10)) and $FFFF;
end;
end;
HFisk := (HFisk xor $71DB) and $FFFF;
HFisk := (HFisk xor ((HFisk and $FFFF) shr 8)) and $FFFF;
for pSdQr := 0 to 2 do
begin
for clrza := 0 to 2 do
begin
HFisk := ((HFisk and $FFFF) - lFOKB) and $FFFF;
end;
HFisk := (HFisk xor $FFFF) and $FFFF;
for GPvNR := 0 to 2 do
begin
HFisk := (HFisk xor lFOKB) and $FFFF;
HFisk := (HFisk xor $FFFF) and $FFFF;
end;
end;
mySecret[lFOKB] := WideChar(HFisk);
end;
ShowMessage(mySecret);Java encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Java]
// myJavaPassword = "Very secret password! QWERTY"
String myJavaPassword = "";
int LcnEg[] = { 0x8DEC, 0x1C11, 0x38B7, 0x7266, 0xE77C, 0xD369, 0xA92B, 0x6FC7,
0xF70E, 0x331E, 0xEC3C, 0xF379, 0x0CF7, 0x51F2, 0x9BEC, 0x47EA,
0x3008, 0xA052, 0x411F, 0x834F, 0x09B7, 0x16F6, 0x36CC, 0x7088,
0x1D71, 0x75E2, 0x6445, 0x9E8B };
for (int syzDT = 0, ZAfcE = 0; syzDT < 28; syzDT++)
{
ZAfcE = LcnEg[syzDT];
ZAfcE = (((ZAfcE & 0xFFFF) >>> 13) | ((ZAfcE & 0xFFFF) << 3)) & 0xFFFF;
ZAfcE = (((ZAfcE & 0xFFFF) >>> (syzDT % 16)) | ((ZAfcE & 0xFFFF) << (16 - (syzDT % 16)))) & 0xFFFF;
ZAfcE = (((~(ZAfcE & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
ZAfcE = (((ZAfcE & 0xFFFF) >>> 8) | ((ZAfcE & 0xFFFF) << 8)) & 0xFFFF;
for (int gyKZB = 0; gyKZB < 3; gyKZB++)
{
ZAfcE = ((ZAfcE & 0xFFFF) - 0xAE0D) & 0xFFFF;
}
ZAfcE = ((ZAfcE & 0xFFFF) + syzDT) & 0xFFFF;
for (int KnuGq = 0; KnuGq < 4; KnuGq++)
{
for (int kbnLT = 0; kbnLT < 4; kbnLT++)
{
ZAfcE = (((ZAfcE & 0xFFFF) >>> 8) | ((ZAfcE & 0xFFFF) << 8)) & 0xFFFF;
}
ZAfcE = (ZAfcE ^ syzDT) & 0xFFFF;
}
ZAfcE = (((ZAfcE & 0xFFFF) >>> 8) | ((ZAfcE & 0xFFFF) << 8)) & 0xFFFF;
for (int oVJfW = 0; oVJfW < 3; oVJfW++)
{
ZAfcE = (ZAfcE ^ 0xC49D) & 0xFFFF;
for (int LzJBK = 0; LzJBK < 2; LzJBK++)
{
ZAfcE = ((ZAfcE & 0xFFFF) - 1) & 0xFFFF;
}
}
for (int JKcZp = 0; JKcZp < 2; JKcZp++)
{
ZAfcE = (ZAfcE ^ syzDT) & 0xFFFF;
for (int kvRTO = 0; kvRTO < 2; kvRTO++)
{
for (int uFglb = 0; uFglb < 2; uFglb++)
{
ZAfcE = (((ZAfcE & 0xFFFF) << 7) | ((ZAfcE & 0xFFFF) >>> 9)) & 0xFFFF;
}
ZAfcE = (ZAfcE ^ 0xFFFF) & 0xFFFF;
}
}
ZAfcE = ((ZAfcE & 0xFFFF) + 0x4453) & 0xFFFF;
ZAfcE = (((ZAfcE & 0xFFFF) >>> 8) | ((ZAfcE & 0xFFFF) << 8)) & 0xFFFF;
myJavaPassword = myJavaPassword + (char)(ZAfcE & 0xFFFF);
}
System.out.println(myJavaPassword);Kotlin encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Kotlin]
// kotlinSecret = "Kotlin on the JVM"
var kotlinSecret: String = ""
val MapNJ: IntArray = intArrayOf( 0x4B2E, 0x0223, 0xC7ED, 0x4032, 0x96E3, 0x7865, 0x23EB, 0x599C,
0xC383, 0x264E, 0x5F09, 0x7EFE, 0xA113, 0xA2A3, 0x00E5, 0x780D,
0x8E55 )
var Qtqma: Int = 0
for (LZjJi in 0 until 17)
{
Qtqma = MapNJ[LZjJi]
Qtqma = ((Qtqma and 0xFFFF) + 0xA521) and 0xFFFF
Qtqma = (Qtqma xor (((Qtqma and 0xFFFF) shl 10) and 0xFFFF)) and 0xFFFF
for (rZUBD in 0 until 4)
{
for (ZXqdA in 0 until 2)
{
Qtqma = (((Qtqma and 0xFFFF) shr (LZjJi % 16)) or ((Qtqma and 0xFFFF) shl (16 - (LZjJi % 16)))) and 0xFFFF
for (vxUnf in 0 until 4)
{
Qtqma = ((Qtqma and 0xFFFF) + 0x0CA9) and 0xFFFF
Qtqma = ((Qtqma and 0xFFFF) - 1) and 0xFFFF
Qtqma = (((Qtqma and 0xFFFF) xor 0xFFFF) + 1) and 0xFFFF
}
}
for (VawkG in 0 until 3)
{
Qtqma = ((Qtqma and 0xFFFF) - LZjJi) and 0xFFFF
Qtqma = ((Qtqma and 0xFFFF) + 0xC4AF) and 0xFFFF
for (JnHMU in 0 until 2)
{
Qtqma = (((Qtqma and 0xFFFF) shl 11) or ((Qtqma and 0xFFFF) shr 5)) and 0xFFFF
Qtqma = (((Qtqma and 0xFFFF) shl (LZjJi % 16)) or ((Qtqma and 0xFFFF) shr (16 - (LZjJi % 16)))) and 0xFFFF
}
}
}
Qtqma = (Qtqma xor 0x1E6F) and 0xFFFF
Qtqma = (Qtqma xor LZjJi) and 0xFFFF
Qtqma = (((Qtqma and 0xFFFF) shl (LZjJi % 16)) or ((Qtqma and 0xFFFF) shr (16 - (LZjJi % 16)))) and 0xFFFF
Qtqma = ((Qtqma and 0xFFFF) - 1) and 0xFFFF
for (DBMXv in 0 until 4)
{
Qtqma = (((Qtqma and 0xFFFF) shr (LZjJi % 16)) or ((Qtqma and 0xFFFF) shl (16 - (LZjJi % 16)))) and 0xFFFF
for (SvQUI in 0 until 3)
{
Qtqma = (Qtqma xor ((Qtqma and 0xFFFF) shr 10)) and 0xFFFF
}
Qtqma = ((Qtqma and 0xFFFF) - LZjJi) and 0xFFFF
}
for (wIdsO in 0 until 4)
{
for (bQekV in 0 until 3)
{
for (ybGvH in 0 until 2)
{
Qtqma = ((Qtqma and 0xFFFF) - 0xC2FD) and 0xFFFF
}
Qtqma = ((Qtqma and 0xFFFF) - 1) and 0xFFFF
}
for (FbYSu in 0 until 2)
{
Qtqma = (((Qtqma and 0xFFFF) shl 4) or ((Qtqma and 0xFFFF) shr 12)) and 0xFFFF
for (FlDtI in 0 until 4)
{
Qtqma = ((Qtqma and 0xFFFF) + 0xDAE9) and 0xFFFF
Qtqma = ((Qtqma and 0xFFFF) - 1) and 0xFFFF
}
}
for (MFZJI in 0 until 3)
{
Qtqma = (Qtqma xor 0x4B9F) and 0xFFFF
}
}
for (aIwem in 0 until 2)
{
Qtqma = ((Qtqma and 0xFFFF) - 1) and 0xFFFF
Qtqma = (Qtqma xor LZjJi) and 0xFFFF
Qtqma = ((Qtqma and 0xFFFF) - LZjJi) and 0xFFFF
}
for (zEwAM in 0 until 4)
{
Qtqma = (((Qtqma and 0xFFFF) shr 1) or ((Qtqma and 0xFFFF) shl 15)) and 0xFFFF
}
for (ygZUD in 0 until 2)
{
for (jgfsh in 0 until 2)
{
for (bwAuM in 0 until 3)
{
Qtqma = ((Qtqma and 0xFFFF) - LZjJi) and 0xFFFF
Qtqma = (Qtqma xor 0xA8C1) and 0xFFFF
}
}
}
for (SmKCk in 0 until 2)
{
Qtqma = ((Qtqma and 0xFFFF) - 0x2E59) and 0xFFFF
Qtqma = (((Qtqma and 0xFFFF) shr 8) or ((Qtqma and 0xFFFF) shl 8)) and 0xFFFF
for (nFtXV in 0 until 4)
{
Qtqma = ((Qtqma and 0xFFFF) + 0xB7F5) and 0xFFFF
}
}
for (lmKPC in 0 until 4)
{
for (xrXVo in 0 until 4)
{
Qtqma = (((Qtqma and 0xFFFF) shl (LZjJi % 16)) or ((Qtqma and 0xFFFF) shr (16 - (LZjJi % 16)))) and 0xFFFF
}
for (eFaSv in 0 until 2)
{
for (zauAC in 0 until 4)
{
Qtqma = (((Qtqma and 0xFFFF) xor 0xFFFF) + 1) and 0xFFFF
}
for (HOFwY in 0 until 3)
{
Qtqma = (Qtqma xor ((Qtqma and 0xFFFF) shr 15)) and 0xFFFF
Qtqma = (Qtqma xor 0x249B) and 0xFFFF
Qtqma = (((Qtqma and 0xFFFF) shr 8) or ((Qtqma and 0xFFFF) shl 8)) and 0xFFFF
}
Qtqma = (((Qtqma and 0xFFFF) shr (LZjJi % 16)) or ((Qtqma and 0xFFFF) shl (16 - (LZjJi % 16)))) and 0xFFFF
}
}
for (Kheuf in 0 until 3)
{
Qtqma = (Qtqma xor LZjJi) and 0xFFFF
for (cZgxP in 0 until 2)
{
Qtqma = (Qtqma xor ((Qtqma and 0xFFFF) shr 12)) and 0xFFFF
Qtqma = ((Qtqma and 0xFFFF) - LZjJi) and 0xFFFF
}
for (UDeIb in 0 until 2)
{
Qtqma = (((Qtqma and 0xFFFF) shr (LZjJi % 16)) or ((Qtqma and 0xFFFF) shl (16 - (LZjJi % 16)))) and 0xFFFF
Qtqma = (Qtqma xor LZjJi) and 0xFFFF
}
}
kotlinSecret += (Qtqma and 0xFFFF).toChar()
}
println(kotlinSecret)Ruby encryption (UNICODE example)
# encrypted with https://www.stringencrypt.com (v1.5.0) [Ruby]
# ruby = "Ruby on rails"
ruby = [ 0x441E, 0x69DE, 0xE834, 0x7022, 0x2CEA, 0x5753, 0x7FCC, 0x4F84,
0x6E7B, 0xC534, 0x8EF9, 0xA4E7, 0xD30C ]
ruby.each_with_index do |qawdj, vdyrt|
4.times do
qawdj = ((qawdj & 0xFFFF) - vdyrt) & 0xFFFF
qawdj = ((qawdj & 0xFFFF) + 0xD208) & 0xFFFF
qawdj = (((qawdj & 0xFFFF) >> 3) | ((qawdj & 0xFFFF) << 13)) & 0xFFFF
end
qawdj = (((qawdj & 0xFFFF) >> 8) | ((qawdj & 0xFFFF) << 8)) & 0xFFFF
qawdj = (((qawdj & 0xFFFF) >> 8) | ((qawdj & 0xFFFF) << 8)) & 0xFFFF
3.times do
qawdj = ((qawdj & 0xFFFF) + 0x1812) & 0xFFFF
qawdj = (((qawdj & 0xFFFF) << 12) | ((qawdj & 0xFFFF) >> 4)) & 0xFFFF
end
qawdj = (((qawdj & 0xFFFF) >> (vdyrt % 16)) | ((qawdj & 0xFFFF) << (16 - (vdyrt % 16)))) & 0xFFFF
qawdj = ((qawdj & 0xFFFF) + vdyrt) & 0xFFFF
qawdj = (((~(qawdj & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF
qawdj = (((qawdj & 0xFFFF) << 7) | ((qawdj & 0xFFFF) >> 9)) & 0xFFFF
qawdj = (qawdj ^ 0xF8E7) & 0xFFFF
qawdj = (((qawdj & 0xFFFF) >> (vdyrt % 16)) | ((qawdj & 0xFFFF) << (16 - (vdyrt % 16)))) & 0xFFFF
3.times do
qawdj = (((qawdj & 0xFFFF) >> 8) | ((qawdj & 0xFFFF) << 8)) & 0xFFFF
qawdj = ((qawdj & 0xFFFF) + 0x2B01) & 0xFFFF
end
2.times do
4.times do
3.times do
qawdj = (qawdj ^ (((qawdj & 0xFFFF) << 15) & 0xFFFF)) & 0xFFFF
end
end
2.times do
qawdj = (((qawdj & 0xFFFF) >> 15) | ((qawdj & 0xFFFF) << 1)) & 0xFFFF
4.times do
qawdj = (qawdj ^ ((qawdj & 0xFFFF) >> 8)) & 0xFFFF
end
qawdj = (qawdj ^ (((qawdj & 0xFFFF) << 8) & 0xFFFF)) & 0xFFFF
end
end
3.times do
2.times do
qawdj = ((qawdj & 0xFFFF) + 0xA961) & 0xFFFF
4.times do
qawdj = (qawdj ^ ((qawdj & 0xFFFF) >> 12)) & 0xFFFF
qawdj = (((qawdj & 0xFFFF) >> 8) | ((qawdj & 0xFFFF) << 8)) & 0xFFFF
end
qawdj = ((qawdj & 0xFFFF) + 0x95E6) & 0xFFFF
end
qawdj = (qawdj ^ 0xFFFF) & 0xFFFF
end
qawdj = (((qawdj & 0xFFFF) << 11) | ((qawdj & 0xFFFF) >> 5)) & 0xFFFF
4.times do
2.times do
qawdj = (((qawdj & 0xFFFF) << (vdyrt % 16)) | ((qawdj & 0xFFFF) >> (16 - (vdyrt % 16)))) & 0xFFFF
4.times do
qawdj = ((qawdj & 0xFFFF) - 1) & 0xFFFF
end
end
qawdj = ((qawdj & 0xFFFF) + 1) & 0xFFFF
end
ruby[vdyrt] = qawdj & 0xFFFF
end
ruby = ruby.pack('v*').force_encoding('UTF-16LE').encode('UTF-8')
puts rubyPython encryption (UNICODE example)
Plain text Python string encryption
cute_wabbit = "A little girl goes into a pet show and asks for a wabbit... http..."to:
# encrypted with https://www.stringencrypt.com (v1.5.0) [Python]
# -*- coding: utf-8 -*-
# cute_wabbit = "A little girl goes into a pet show and asks for a wabbit... http..."
cute_wabbit = [0xAC75, 0xD6D1, 0xC0F3, 0xCE7E, 0xE4E9, 0x5E85, 0x6E48, 0xB038,
0x9325, 0xD141, 0x2CAE, 0x2680, 0x7E27, 0x6E40, 0x8CDF, 0x9840,
0xBCB0, 0x75A0, 0xAD1A, 0x09AC, 0x9D01, 0x35D2, 0xD712, 0x6F69,
0xA53D, 0x75B8, 0xAE25, 0x266F, 0xEA84, 0xCA81, 0x6855, 0x6BB6,
0x9BE8, 0xC002, 0xA622, 0x709E, 0x9732, 0x48F4, 0x3E73, 0x6AD4,
0x135C, 0xD181, 0x65E9, 0x220A, 0xFE25, 0x9F0D, 0x82B1, 0x0C97,
0x4567, 0xAF11, 0xDC07, 0x98E6, 0x3202, 0x5B80, 0x923C, 0xE3A9,
0x9EF2, 0xF11A, 0xEFA1, 0x70EB, 0x5BCF, 0xC56D, 0x1D7B, 0x638C,
0xE11D, 0x9BD2, 0x513F]
for qoPms in range(67):
jmsGR = cute_wabbit[qoPms]
jmsGR = ((jmsGR & 0xFFFF) + 0x97C3) & 0xFFFF
jmsGR = (jmsGR ^ ((jmsGR & 0xFFFF) >> 13)) & 0xFFFF
for znegy in range(2):
jmsGR = (((jmsGR & 0xFFFF) >> (qoPms % 16)) | ((jmsGR & 0xFFFF) << (16 - (qoPms % 16)))) & 0xFFFF
for dwJcX in range(3):
jmsGR = ((jmsGR & 0xFFFF) + 1) & 0xFFFF
jmsGR = (jmsGR ^ 0xFFFF) & 0xFFFF
for QpYFt in range(4):
jmsGR = (((jmsGR & 0xFFFF) >> (qoPms % 16)) | ((jmsGR & 0xFFFF) << (16 - (qoPms % 16)))) & 0xFFFF
jmsGR = (jmsGR ^ 0x6701) & 0xFFFF
jmsGR = (((jmsGR & 0xFFFF) >> 5) | ((jmsGR & 0xFFFF) << 11)) & 0xFFFF
for TUYrh in range(4):
jmsGR = (((jmsGR & 0xFFFF) << (qoPms % 16)) | ((jmsGR & 0xFFFF) >> (16 - (qoPms % 16)))) & 0xFFFF
for HdbmR in range(4):
jmsGR = ((jmsGR & 0xFFFF) - 1) & 0xFFFF
for lrOZq in range(4):
jmsGR = (((~(jmsGR & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF
for VqmkO in range(2):
for ZIsub in range(4):
jmsGR = ((jmsGR & 0xFFFF) + 1) & 0xFFFF
jmsGR = (((jmsGR & 0xFFFF) << (qoPms % 16)) | ((jmsGR & 0xFFFF) >> (16 - (qoPms % 16)))) & 0xFFFF
for XznKW in range(4):
jmsGR = (jmsGR ^ qoPms) & 0xFFFF
jmsGR = (((jmsGR & 0xFFFF) >> 8) | ((jmsGR & 0xFFFF) << 8)) & 0xFFFF
jmsGR = ((jmsGR & 0xFFFF) - 1) & 0xFFFF
for AflZi in range(2):
for XJsoA in range(4):
for bfcXt in range(2):
jmsGR = ((jmsGR & 0xFFFF) + qoPms) & 0xFFFF
jmsGR = (jmsGR ^ 0x5166) & 0xFFFF
jmsGR = ((jmsGR & 0xFFFF) - 1) & 0xFFFF
jmsGR = (((jmsGR & 0xFFFF) << 12) | ((jmsGR & 0xFFFF) >> 4)) & 0xFFFF
jmsGR = (jmsGR ^ 0x0D9D) & 0xFFFF
for iaOnJ in range(3):
jmsGR = ((jmsGR & 0xFFFF) + 1) & 0xFFFF
jmsGR = (((jmsGR & 0xFFFF) << 9) | ((jmsGR & 0xFFFF) >> 7)) & 0xFFFF
for bdijX in range(4):
jmsGR = ((jmsGR & 0xFFFF) + 1) & 0xFFFF
for QRKMA in range(3):
for yOQqG in range(3):
jmsGR = (jmsGR ^ qoPms) & 0xFFFF
for Rvjzn in range(2):
jmsGR = ((jmsGR & 0xFFFF) + 1) & 0xFFFF
jmsGR = ((jmsGR & 0xFFFF) + qoPms) & 0xFFFF
jmsGR = ((jmsGR & 0xFFFF) - 0xF65D) & 0xFFFF
jmsGR = ((jmsGR & 0xFFFF) - 1) & 0xFFFF
for euRAN in range(2):
jmsGR = (jmsGR ^ 0xFFFF) & 0xFFFF
jmsGR = (((jmsGR & 0xFFFF) << 8) | ((jmsGR & 0xFFFF) >> 8)) & 0xFFFF
jmsGR = (jmsGR ^ ((jmsGR & 0xFFFF) >> 11)) & 0xFFFF
for woETk in range(3):
for YJSUn in range(4):
jmsGR = ((jmsGR & 0xFFFF) + 1) & 0xFFFF
cute_wabbit[qoPms] = jmsGR
cute_wabbit = ''.join(chr(jmsGR & 0xFFFF) for jmsGR in cute_wabbit)
del qoPms, jmsGR
print(cute_wabbit)PHP encryption (ANSI example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [PHP]
// Encoding: Windows-1250 or match your source file
// $secret = "PHP string encryption"
$secret = [ 0x8E, 0x40, 0x56, 0xAE, 0x7A, 0x0B, 0x1D, 0x51,
0x5D, 0x63, 0x13, 0xDA, 0x6E, 0x3F, 0xDB, 0x5E,
0xB9, 0x79, 0x1F, 0xA6, 0x17 ];
$DGEPd = 0;
for ($PBbql = 0; $PBbql < 21; $PBbql++)
{
$DGEPd = $secret[$PBbql];
for ($pNjYM = 0; $pNjYM < 4; $pNjYM++)
{
$DGEPd = ($DGEPd ^ 0x3D) & 0xFF;
$DGEPd = (((~($DGEPd & 0xFF)) & 0xFF) + 1) & 0xFF;
}
$DGEPd = ($DGEPd ^ 0xB6) & 0xFF;
$DGEPd = ($DGEPd ^ $PBbql) & 0xFF;
for ($XnxLS = 0; $XnxLS < 2; $XnxLS++)
{
for ($qoZCp = 0; $qoZCp < 4; $qoZCp++)
{
$DGEPd = ((($DGEPd & 0xFF) >> 7) | (($DGEPd & 0xFF) << 1)) & 0xFF;
}
for ($CsgJZ = 0; $CsgJZ < 4; $CsgJZ++)
{
for ($VwNLz = 0; $VwNLz < 3; $VwNLz++)
{
$DGEPd = ($DGEPd ^ ((($DGEPd & 0xFF) << 4) & 0xFF)) & 0xFF;
$DGEPd = ((($DGEPd & 0xFF) >> 4) | (($DGEPd & 0xFF) << 4)) & 0xFF;
}
$DGEPd = (($DGEPd & 0xFF) + 1) & 0xFF;
}
}
$DGEPd = (($DGEPd & 0xFF) + 0xD0) & 0xFF;
$DGEPd = ((($DGEPd & 0xFF) >> 4) | (($DGEPd & 0xFF) << 4)) & 0xFF;
for ($cUyMk = 0; $cUyMk < 3; $cUyMk++)
{
$DGEPd = (($DGEPd & 0xFF) + 1) & 0xFF;
$DGEPd = ((($DGEPd & 0xFF) << ($PBbql % 8)) | (($DGEPd & 0xFF) >> (8 - ($PBbql % 8)))) & 0xFF;
}
for ($UmJxX = 0; $UmJxX < 2; $UmJxX++)
{
for ($RGWvx = 0; $RGWvx < 4; $RGWvx++)
{
for ($xNBhy = 0; $xNBhy < 4; $xNBhy++)
{
$DGEPd = (($DGEPd & 0xFF) - 0x27) & 0xFF;
}
}
}
$DGEPd = (($DGEPd & 0xFF) + 1) & 0xFF;
for ($lJFgB = 0; $lJFgB < 3; $lJFgB++)
{
$DGEPd = ($DGEPd ^ $PBbql) & 0xFF;
$DGEPd = ((($DGEPd & 0xFF) << ($PBbql % 8)) | (($DGEPd & 0xFF) >> (8 - ($PBbql % 8)))) & 0xFF;
for ($nGAaX = 0; $nGAaX < 2; $nGAaX++)
{
for ($RMrYp = 0; $RMrYp < 4; $RMrYp++)
{
$DGEPd = ($DGEPd ^ 0xFF) & 0xFF;
}
for ($pUZjW = 0; $pUZjW < 4; $pUZjW++)
{
$DGEPd = (($DGEPd & 0xFF) - $PBbql) & 0xFF;
}
$DGEPd = ($DGEPd ^ (($DGEPd & 0xFF) >> 6)) & 0xFF;
}
}
$DGEPd = ($DGEPd ^ 0x27) & 0xFF;
for ($QHPSD = 0; $QHPSD < 3; $QHPSD++)
{
$DGEPd = (($DGEPd & 0xFF) + 0x6C) & 0xFF;
}
for ($PquxI = 0; $PquxI < 4; $PquxI++)
{
$DGEPd = (($DGEPd & 0xFF) - 1) & 0xFF;
for ($yCWuE = 0; $yCWuE < 2; $yCWuE++)
{
$DGEPd = (($DGEPd & 0xFF) - 0xAF) & 0xFF;
for ($DFgxE = 0; $DFgxE < 4; $DFgxE++)
{
$DGEPd = (($DGEPd & 0xFF) + 0x1D) & 0xFF;
$DGEPd = ($DGEPd ^ 0xFF) & 0xFF;
}
$DGEPd = (($DGEPd & 0xFF) + 1) & 0xFF;
}
for ($uadXk = 0; $uadXk < 4; $uadXk++)
{
$DGEPd = ($DGEPd ^ $PBbql) & 0xFF;
}
}
$secret[$PBbql] = $DGEPd;
}
$secret = implode('', array_map(function ($c) { return chr($c & 0xFF); }, $secret));
echo secret;Dart encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Dart]
// dartSecret = "Dart null-safe strings"
String dartSecret = '\u{8BBE}\u{07F5}\u{900D}\u{47C5}\u{6C7D}\u{3986}\u{801A}\u{B154}' +
'\u{A013}\u{33CF}\u{5586}\u{B661}\u{329E}\u{343A}\u{AC1D}\u{9752}' +
'\u{F397}\u{36CA}\u{258B}\u{4C90}\u{6759}\u{4238}';
for (int eHdaK = 0, xNhfY = 0; eHdaK < 22; eHdaK++)
{
xNhfY = (dartSecret.codeUnitAt(eHdaK));
for (int UkmTW = 0; UkmTW < 3; UkmTW++)
{
xNhfY = ((xNhfY & 0xFFFF) + eHdaK) & 0xFFFF;
xNhfY = ((xNhfY & 0xFFFF) + 1) & 0xFFFF;
}
for (int xTQZL = 0; xTQZL < 2; xTQZL++)
{
xNhfY = (((xNhfY & 0xFFFF) >> (eHdaK % 16)) | ((xNhfY & 0xFFFF) << (16 - (eHdaK % 16)))) & 0xFFFF;
xNhfY = ((xNhfY & 0xFFFF) + 0x6486) & 0xFFFF;
}
for (int TnAxM = 0; TnAxM < 4; TnAxM++)
{
for (int rnkwZ = 0; rnkwZ < 2; rnkwZ++)
{
xNhfY = (((xNhfY & 0xFFFF) >> (eHdaK % 16)) | ((xNhfY & 0xFFFF) << (16 - (eHdaK % 16)))) & 0xFFFF;
xNhfY = ((xNhfY & 0xFFFF) - eHdaK) & 0xFFFF;
}
for (int fxhZW = 0; fxhZW < 4; fxhZW++)
{
xNhfY = (xNhfY ^ 0x92F4) & 0xFFFF;
}
xNhfY = ((xNhfY & 0xFFFF) - 1) & 0xFFFF;
}
xNhfY = (xNhfY ^ ((xNhfY & 0xFFFF) >> 10)) & 0xFFFF;
for (int nozUF = 0; nozUF < 3; nozUF++)
{
xNhfY = (((xNhfY & 0xFFFF) << (eHdaK % 16)) | ((xNhfY & 0xFFFF) >> (16 - (eHdaK % 16)))) & 0xFFFF;
}
xNhfY = (xNhfY ^ 0x7948) & 0xFFFF;
for (int gROwa = 0; gROwa < 3; gROwa++)
{
xNhfY = (((~(xNhfY & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
for (int GyLBD = 0; GyLBD < 4; GyLBD++)
{
for (int xnTDg = 0; xnTDg < 4; xnTDg++)
{
xNhfY = ((xNhfY & 0xFFFF) + eHdaK) & 0xFFFF;
}
for (int czReq = 0; czReq < 3; czReq++)
{
xNhfY = (((~(xNhfY & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
xNhfY = (((xNhfY & 0xFFFF) >> 8) | ((xNhfY & 0xFFFF) << 8)) & 0xFFFF;
xNhfY = (((~(xNhfY & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
}
xNhfY = (((xNhfY & 0xFFFF) >> 7) | ((xNhfY & 0xFFFF) << 9)) & 0xFFFF;
}
}
xNhfY = (xNhfY ^ 0x1B95) & 0xFFFF;
xNhfY = (xNhfY ^ ((xNhfY & 0xFFFF) >> 10)) & 0xFFFF;
for (int JtOdF = 0; JtOdF < 4; JtOdF++)
{
for (int VYzxK = 0; VYzxK < 4; VYzxK++)
{
for (int gnUAS = 0; gnUAS < 2; gnUAS++)
{
xNhfY = ((xNhfY & 0xFFFF) + 0xF25D) & 0xFFFF;
xNhfY = (((xNhfY & 0xFFFF) << 5) | ((xNhfY & 0xFFFF) >> 11)) & 0xFFFF;
xNhfY = ((xNhfY & 0xFFFF) + eHdaK) & 0xFFFF;
}
}
for (int NFGjY = 0; NFGjY < 2; NFGjY++)
{
xNhfY = (xNhfY ^ 0xFFFF) & 0xFFFF;
for (int mZcBl = 0; mZcBl < 4; mZcBl++)
{
xNhfY = ((xNhfY & 0xFFFF) + eHdaK) & 0xFFFF;
xNhfY = (xNhfY ^ (((xNhfY & 0xFFFF) << 10) & 0xFFFF)) & 0xFFFF;
}
}
}
xNhfY = (((xNhfY & 0xFFFF) >> (eHdaK % 16)) | ((xNhfY & 0xFFFF) << (16 - (eHdaK % 16)))) & 0xFFFF;
xNhfY = (((~(xNhfY & 0xFFFF)) & 0xFFFF) + 1) & 0xFFFF;
// TODO: immutable String; use StringBuffer or runes for production
dartSecret = dartSecret.substring(0, eHdaK) + String.fromCharCode(xNhfY & 0xFFFF) + dartSecret.substring(eHdaK + 1);
}
print(dartSecret);Go encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Go]
import (
"fmt"
"unicode/utf16"
)
// secretGo = "Go string encryption"
var IdORV [21]uint16
IdORV[0] = 0x05BA IdORV[10] = 0xD7DB IdORV[12] = 0x9261 IdORV[7] = 0xF7B2
IdORV[3] = 0x353D IdORV[15] = 0x8969 IdORV[20] = 0x4A86 IdORV[6] = 0x25C5
IdORV[2] = 0xFB61 IdORV[18] = 0x97E2 IdORV[17] = 0xEBA7 IdORV[16] = 0xDD8D
IdORV[19] = 0xE53D IdORV[11] = 0xF7E8 IdORV[13] = 0x2604 IdORV[4] = 0xC896
IdORV[1] = 0x318A IdORV[5] = 0xE1D7 IdORV[9] = 0xBF59 IdORV[14] = 0x67B5
IdORV[8] = 0x3978
var cbmGh uint16 = 0
for ywkYl := 0; ywkYl < 21; ywkYl++ {
cbmGh = uint16(IdORV[ywkYl])
cbmGh = ((^(cbmGh & uint16(0xFFFF)) & uint16(0xFFFF)) + uint16(1)) & uint16(0xFFFF)
for KzBpw := 0; KzBpw < 4; KzBpw++ {
for Vpmdv := 0; Vpmdv < 2; Vpmdv++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) >> uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) << uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
for RvcuI := 0; RvcuI < 2; RvcuI++ {
cbmGh = (cbmGh ^ uint16(0xEBA1)) & uint16(0xFFFF)
cbmGh = ((^(cbmGh & uint16(0xFFFF)) & uint16(0xFFFF)) + uint16(1)) & uint16(0xFFFF)
}
}
}
for mDHtT := 0; mDHtT < 3; mDHtT++ {
cbmGh = (cbmGh ^ uint16(ywkYl)) & uint16(0xFFFF)
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(0xBE3D)) & uint16(0xFFFF)
}
for OQUSg := 0; OQUSg < 3; OQUSg++ {
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(ywkYl)) & uint16(0xFFFF)
for EScqL := 0; EScqL < 2; EScqL++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) >> 4) | ((cbmGh & uint16(0xFFFF)) << 12)) & uint16(0xFFFF)
}
cbmGh = (cbmGh ^ uint16(0xFFFF)) & uint16(0xFFFF)
}
cbmGh = (((cbmGh & uint16(0xFFFF)) << uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) >> uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
cbmGh = (((cbmGh & uint16(0xFFFF)) >> 8) | ((cbmGh & uint16(0xFFFF)) << 8)) & uint16(0xFFFF)
for FvKPx := 0; FvKPx < 2; FvKPx++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) >> uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) << uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
for sPyek := 0; sPyek < 2; sPyek++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) << 15) | ((cbmGh & uint16(0xFFFF)) >> 1)) & uint16(0xFFFF)
cbmGh = (((cbmGh & uint16(0xFFFF)) >> uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) << uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
}
for gmqae := 0; gmqae < 4; gmqae++ {
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(0x3DA6)) & uint16(0xFFFF)
for SqVjo := 0; SqVjo < 3; SqVjo++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) << 1) | ((cbmGh & uint16(0xFFFF)) >> 15)) & uint16(0xFFFF)
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(1)) & uint16(0xFFFF)
cbmGh = (((cbmGh & uint16(0xFFFF)) << 8) | ((cbmGh & uint16(0xFFFF)) >> 8)) & uint16(0xFFFF)
}
}
}
for zOIyq := 0; zOIyq < 2; zOIyq++ {
cbmGh = (cbmGh ^ uint16(ywkYl)) & uint16(0xFFFF)
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(ywkYl)) & uint16(0xFFFF)
}
cbmGh = (((cbmGh & uint16(0xFFFF)) << uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) >> uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
cbmGh = (cbmGh ^ ((cbmGh & uint16(0xFFFF)) >> 12)) & uint16(0xFFFF)
for Jerya := 0; Jerya < 4; Jerya++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) >> uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) << uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
cbmGh = (((cbmGh & uint16(0xFFFF)) << 8) | ((cbmGh & uint16(0xFFFF)) >> 8)) & uint16(0xFFFF)
for sFYvt := 0; sFYvt < 2; sFYvt++ {
for Bpuqo := 0; Bpuqo < 4; Bpuqo++ {
cbmGh = ((cbmGh & uint16(0xFFFF)) + uint16(0x63BE)) & uint16(0xFFFF)
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(1)) & uint16(0xFFFF)
}
cbmGh = ((cbmGh & uint16(0xFFFF)) + uint16(ywkYl)) & uint16(0xFFFF)
}
}
for EsPno := 0; EsPno < 2; EsPno++ {
cbmGh = ((cbmGh & uint16(0xFFFF)) + uint16(0x6C88)) & uint16(0xFFFF)
for NoeXP := 0; NoeXP < 4; NoeXP++ {
cbmGh = ((^(cbmGh & uint16(0xFFFF)) & uint16(0xFFFF)) + uint16(1)) & uint16(0xFFFF)
cbmGh = (((cbmGh & uint16(0xFFFF)) >> 8) | ((cbmGh & uint16(0xFFFF)) << 8)) & uint16(0xFFFF)
cbmGh = (cbmGh ^ (((cbmGh & uint16(0xFFFF)) << 12) & uint16(0xFFFF))) & uint16(0xFFFF)
}
cbmGh = (((cbmGh & uint16(0xFFFF)) >> uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) << uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
}
for PTpkN := 0; PTpkN < 4; PTpkN++ {
cbmGh = ((cbmGh & uint16(0xFFFF)) + uint16(1)) & uint16(0xFFFF)
}
for wMPIf := 0; wMPIf < 2; wMPIf++ {
cbmGh = (((cbmGh & uint16(0xFFFF)) >> uint(ywkYl % 16)) | ((cbmGh & uint16(0xFFFF)) << uint(16 - (ywkYl % 16)))) & uint16(0xFFFF)
cbmGh = (((cbmGh & uint16(0xFFFF)) << 9) | ((cbmGh & uint16(0xFFFF)) >> 7)) & uint16(0xFFFF)
for Fqhur := 0; Fqhur < 4; Fqhur++ {
cbmGh = ((cbmGh & uint16(0xFFFF)) - uint16(0x132C)) & uint16(0xFFFF)
cbmGh = ((cbmGh & uint16(0xFFFF)) + uint16(1)) & uint16(0xFFFF)
}
}
IdORV[ywkYl] = uint16(cbmGh)
}
secretGo := string(utf16.Decode(IdORV[:]))
fmt.Println(secretGo)Rust encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Rust]
// secret = "Rust string encryption"
let mut ZaoBk: [u16; 23] = [0u16; 23];
ZaoBk[7] = 0x1051; ZaoBk[12] = 0xA2E0; ZaoBk[13] = 0x500D; ZaoBk[1] = 0x92D4;
ZaoBk[18] = 0xEB9E; ZaoBk[9] = 0x4C0C; ZaoBk[0] = 0x946F; ZaoBk[19] = 0x5D14;
ZaoBk[14] = 0x8C80; ZaoBk[22] = 0xCE49; ZaoBk[11] = 0x694D; ZaoBk[5] = 0x83CE;
ZaoBk[20] = 0x37A6; ZaoBk[6] = 0xE77D; ZaoBk[4] = 0x5888; ZaoBk[15] = 0x8741;
ZaoBk[2] = 0x958E; ZaoBk[17] = 0xE60C; ZaoBk[16] = 0xCEB0; ZaoBk[10] = 0xF880;
ZaoBk[3] = 0xF6E5; ZaoBk[8] = 0x81CB; ZaoBk[21] = 0xC00E;
let mut nqUGQ: u16 = 0;
for snfNx in 0..23
{
nqUGQ = ZaoBk[snfNx];
for DRCeJ in 0..3
{
for VLPwO in 0..2
{
nqUGQ = (nqUGQ ^ (((nqUGQ & 0xFFFF).wrapping_shl((8u32) & 15)) & 0xFFFF)) & 0xFFFF;
nqUGQ = (nqUGQ ^ ((nqUGQ & 0xFFFF).wrapping_shr((14u32) & 15))) & 0xFFFF;
for ZbJNQ in 0..3
{
nqUGQ = (nqUGQ & 0xFFFF).wrapping_add(0xE7FA) & 0xFFFF;
}
}
}
for xbozp in 0..4
{
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shl((snfNx as u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shr((16u32).wrapping_sub((snfNx as u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
}
for JYDzH in 0..4
{
for QaNjY in 0..4
{
nqUGQ = (nqUGQ & 0xFFFF).wrapping_sub(1) & 0xFFFF;
nqUGQ = (nqUGQ ^ 0xDF4F) & 0xFFFF;
}
nqUGQ = (nqUGQ ^ ((nqUGQ & 0xFFFF).wrapping_shr((13u32) & 15))) & 0xFFFF;
}
nqUGQ = (nqUGQ & 0xFFFF).wrapping_add(0xC1D6) & 0xFFFF;
for bDPFc in 0..4
{
nqUGQ = ((nqUGQ ^ 0xFFFF).wrapping_add(1)) & 0xFFFF;
}
for GuCTV in 0..3
{
for RNIXt in 0..3
{
nqUGQ = (nqUGQ ^ (((nqUGQ & 0xFFFF).wrapping_shl((14u32) & 15)) & 0xFFFF)) & 0xFFFF;
for ijnWa in 0..4
{
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shr((14u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shl((16u32).wrapping_sub((14u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
nqUGQ = ((nqUGQ ^ 0xFFFF).wrapping_add(1)) & 0xFFFF;
nqUGQ = (nqUGQ ^ 0xFFFF) & 0xFFFF;
}
nqUGQ = (nqUGQ & 0xFFFF).wrapping_add(0xF8AA) & 0xFFFF;
}
nqUGQ = (nqUGQ & 0xFFFF).wrapping_sub(1) & 0xFFFF;
}
nqUGQ = (nqUGQ ^ 0xFFFF) & 0xFFFF;
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shl((1u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shr((16u32).wrapping_sub((1u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
for LaUbu in 0..4
{
for aHhFw in 0..4
{
for EqgMf in 0..3
{
nqUGQ = (nqUGQ ^ (snfNx as u16)) & 0xFFFF;
}
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shr((snfNx as u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shl((16u32).wrapping_sub((snfNx as u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
for bYSgs in 0..2
{
nqUGQ = ((nqUGQ ^ 0xFFFF).wrapping_add(1)) & 0xFFFF;
nqUGQ = (nqUGQ ^ 0x0FD8) & 0xFFFF;
nqUGQ = (nqUGQ ^ 0xFFFF) & 0xFFFF;
}
}
}
for dkTWb in 0..4
{
nqUGQ = (nqUGQ & 0xFFFF).wrapping_add(1) & 0xFFFF;
}
nqUGQ = (nqUGQ & 0xFFFF).wrapping_add(0x02F4) & 0xFFFF;
for HcirN in 0..2
{
for zqcmB in 0..4
{
nqUGQ = (nqUGQ ^ 0xBDF6) & 0xFFFF;
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shl((4u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shr((16u32).wrapping_sub((4u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
}
for zeBCZ in 0..3
{
nqUGQ = (nqUGQ & 0xFFFF).wrapping_add(0x3DF3) & 0xFFFF;
nqUGQ = (nqUGQ ^ 0xFFFF) & 0xFFFF;
}
for XLSda in 0..2
{
for oafFd in 0..4
{
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shr((snfNx as u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shl((16u32).wrapping_sub((snfNx as u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
nqUGQ = ((nqUGQ & 0xFFFF).wrapping_shl((9u32) % 16u32) | (nqUGQ & 0xFFFF).wrapping_shr((16u32).wrapping_sub((9u32) % 16u32).wrapping_rem(16u32))) & 0xFFFF;
nqUGQ = ((nqUGQ ^ 0xFFFF).wrapping_add(1)) & 0xFFFF;
}
}
}
ZaoBk[snfNx] = nqUGQ;
}
let secret = String::from_utf16_lossy(&ZaoBk[..]);
println!("{}", secret);Swift encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Swift]
// swiftSecret = "Swift string encryption"
var swiftSecret: String = ""
var IDqik: [UInt16] = [ 0x3CF5, 0x0432, 0x570D, 0xFF09, 0xE59C, 0xC844, 0xEFBD, 0xF20E,
0x00B3, 0x49E0, 0x5693, 0xB64F, 0xB918, 0xD406, 0xA40A, 0xB2F7,
0x5F21, 0x98EC, 0xAA18, 0x8F12, 0x7169, 0xC144, 0xE12D ]
var nhbgA: UInt16 = 0
for fpLGc in 0..<23
{
nhbgA = UInt16(IDqik[fpLGc])
for _ in 0..<4
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(1)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(fpLGc)) & UInt16(0xFFFF)
nhbgA = (((nhbgA & UInt16(0xFFFF)) << (fpLGc % 16)) | ((nhbgA & UInt16(0xFFFF)) >> (16 - (fpLGc % 16)))) & UInt16(0xFFFF)
}
nhbgA = (nhbgA ^ UInt16(0xD283)) & UInt16(0xFFFF)
nhbgA = (nhbgA ^ UInt16(0xFFFF)) & UInt16(0xFFFF)
for _ in 0..<3
{
nhbgA = (nhbgA ^ UInt16(0x225A)) & UInt16(0xFFFF)
}
for _ in 0..<4
{
nhbgA = (nhbgA ^ ((nhbgA & UInt16(0xFFFF)) >> 13)) & UInt16(0xFFFF)
nhbgA = (((nhbgA & UInt16(0xFFFF)) >> 6) | ((nhbgA & UInt16(0xFFFF)) << 10)) & UInt16(0xFFFF)
for _ in 0..<3
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(1)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(1)) & UInt16(0xFFFF)
}
}
for _ in 0..<3
{
nhbgA = (nhbgA ^ ((nhbgA & UInt16(0xFFFF)) >> 9)) & UInt16(0xFFFF)
for _ in 0..<2
{
for _ in 0..<2
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(fpLGc)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(0xEED7)) & UInt16(0xFFFF)
}
for _ in 0..<2
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(fpLGc)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(1)) & UInt16(0xFFFF)
}
}
nhbgA = (nhbgA ^ (((nhbgA & UInt16(0xFFFF)) << 10) & UInt16(0xFFFF))) & UInt16(0xFFFF)
}
nhbgA = (((~(nhbgA & UInt16(0xFFFF))) & UInt16(0xFFFF)) &+ UInt16(1)) & UInt16(0xFFFF)
for _ in 0..<4
{
nhbgA = (((nhbgA & UInt16(0xFFFF)) >> (fpLGc % 16)) | ((nhbgA & UInt16(0xFFFF)) << (16 - (fpLGc % 16)))) & UInt16(0xFFFF)
for _ in 0..<3
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(1)) & UInt16(0xFFFF)
nhbgA = (((nhbgA & UInt16(0xFFFF)) >> 12) | ((nhbgA & UInt16(0xFFFF)) << 4)) & UInt16(0xFFFF)
for _ in 0..<4
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(0x264C)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(0xE417)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(1)) & UInt16(0xFFFF)
}
}
}
nhbgA = (((nhbgA & UInt16(0xFFFF)) >> (fpLGc % 16)) | ((nhbgA & UInt16(0xFFFF)) << (16 - (fpLGc % 16)))) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(0xA438)) & UInt16(0xFFFF)
for _ in 0..<3
{
for _ in 0..<3
{
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(1)) & UInt16(0xFFFF)
for _ in 0..<3
{
nhbgA = (nhbgA ^ UInt16(fpLGc)) & UInt16(0xFFFF)
nhbgA = (((~(nhbgA & UInt16(0xFFFF))) & UInt16(0xFFFF)) &+ UInt16(1)) & UInt16(0xFFFF)
}
for _ in 0..<2
{
nhbgA = (nhbgA ^ (((nhbgA & UInt16(0xFFFF)) << 13) & UInt16(0xFFFF))) & UInt16(0xFFFF)
}
}
}
nhbgA = (nhbgA ^ UInt16(0x5F00)) & UInt16(0xFFFF)
for _ in 0..<3
{
for _ in 0..<4
{
nhbgA = (nhbgA ^ ((nhbgA & UInt16(0xFFFF)) >> 15)) & UInt16(0xFFFF)
for _ in 0..<2
{
nhbgA = (nhbgA ^ (((nhbgA & UInt16(0xFFFF)) << 10) & UInt16(0xFFFF))) & UInt16(0xFFFF)
}
for _ in 0..<4
{
nhbgA = (nhbgA ^ UInt16(fpLGc)) & UInt16(0xFFFF)
}
}
nhbgA = (nhbgA ^ ((nhbgA & UInt16(0xFFFF)) >> 14)) & UInt16(0xFFFF)
}
nhbgA = ((nhbgA & UInt16(0xFFFF)) &+ UInt16(fpLGc)) & UInt16(0xFFFF)
for _ in 0..<3
{
nhbgA = (((nhbgA & UInt16(0xFFFF)) >> 8) | ((nhbgA & UInt16(0xFFFF)) << 8)) & UInt16(0xFFFF)
nhbgA = ((nhbgA & UInt16(0xFFFF)) &- UInt16(fpLGc)) & UInt16(0xFFFF)
}
IDqik[fpLGc] = UInt16(nhbgA)
swiftSecret = String(decoding: IDqik, as: UTF16.self)
}
print(swiftSecret)Lua encryption (UNICODE example)
-- encrypted with https://www.stringencrypt.com (v1.5.0) [Lua]
-- Requires Lua 5.3+ (bitwise operators: &, |, ~, <<, >>)
-- Unicode: utf8.char() for BMP code points (string.char only accepts 0..255)
-- luaSecret = "Lua string encryption"
local luaSecret = { 0x819A, 0x251F, 0x20EF, 0x2473, 0x3770, 0xACE5, 0x57AC, 0x5FB6,
0xA232, 0x7349, 0xBB95, 0x5CC2, 0xE7B1, 0x8AF8, 0xB07D, 0x80B5,
0x005A, 0x4FE4, 0x76DA, 0x8684, 0xCD7D }
local cBxhf = 0
for JuYFm = 0, 21 - 1 do
cBxhf = luaSecret[JuYFm + 1]
for GweYp = 1, 4 do
cBxhf = (cBxhf ~ (((cBxhf & 0xFFFF) << 11) & 0xFFFF)) & 0xFFFF
cBxhf = (((cBxhf & 0xFFFF) >> 7) | ((cBxhf & 0xFFFF) << 9)) & 0xFFFF
cBxhf = ((cBxhf & 0xFFFF) - 0x08F7) & 0xFFFF
end
cBxhf = (cBxhf ~ ((cBxhf & 0xFFFF) >> 9)) & 0xFFFF
cBxhf = ((((cBxhf & 0xFFFF) >> 8) | ((cBxhf & 0xFFFF) << 8)) & 0xFFFF)
for oJScO = 1, 3 do
cBxhf = (((cBxhf & 0xFFFF) >> (JuYFm % 16)) | ((cBxhf & 0xFFFF) << (16 - (JuYFm % 16)))) & 0xFFFF
for VCOYf = 1, 3 do
for Bozka = 1, 4 do
cBxhf = (cBxhf ~ JuYFm) & 0xFFFF
cBxhf = ((cBxhf & 0xFFFF) + JuYFm) & 0xFFFF
end
end
end
cBxhf = (cBxhf ~ 0xDB0C) & 0xFFFF
cBxhf = ((cBxhf & 0xFFFF) - 1) & 0xFFFF
for OAbZp = 1, 2 do
cBxhf = ((cBxhf & 0xFFFF) + 1) & 0xFFFF
end
for FoYMh = 1, 4 do
cBxhf = ((cBxhf ~ 0xFFFF) & 0xFFFF)
cBxhf = ((cBxhf & 0xFFFF) + 0x1A96) & 0xFFFF
end
cBxhf = (((cBxhf & 0xFFFF) >> (JuYFm % 16)) | ((cBxhf & 0xFFFF) << (16 - (JuYFm % 16)))) & 0xFFFF
cBxhf = ((cBxhf & 0xFFFF) - JuYFm) & 0xFFFF
luaSecret[JuYFm + 1] = cBxhf
end
local SBvyf = {}
for SMmeg = 1, #luaSecret do
SBvyf[SMmeg] = utf8.char((luaSecret[SMmeg] & 0xFFFF))
end
luaSecret = table.concat(SBvyf)
print(luaSecret)Objective-C encryption (UNICODE example)
// encrypted with https://www.stringencrypt.com (v1.5.0) [Objective-C]
// objcSecret = "Objective-C NSString"
unsigned short objcSecret[21];
objcSecret[3] = 0xA888; objcSecret[9] = 0x64FE; objcSecret[4] = 0x0399; objcSecret[8] = 0xC613;
objcSecret[5] = 0x5B69; objcSecret[7] = 0xCAD4; objcSecret[1] = 0xDEC0; objcSecret[18] = 0x7213;
objcSecret[13] = 0xE767; objcSecret[20] = 0xC9C3; objcSecret[0] = 0x76FD; objcSecret[14] = 0xE1CE;
objcSecret[16] = 0x491E; objcSecret[6] = 0x7B59; objcSecret[10] = 0x3FDE; objcSecret[15] = 0xE867;
objcSecret[19] = 0xC3F8; objcSecret[2] = 0x6E4A; objcSecret[11] = 0x77EE; objcSecret[17] = 0x0D46;
objcSecret[12] = 0xDAE8;
for (unsigned int pwrWB = 0, ORZzX = 0; pwrWB < 21; pwrWB++)
{
ORZzX = objcSecret[pwrWB];
for (unsigned int LyZQA = 0; LyZQA < 2; LyZQA++)
{
ORZzX = ((ORZzX & 0xFFFF) + 1) & 0xFFFF;
ORZzX = (ORZzX ^ (((ORZzX & 0xFFFF) << 8) & 0xFFFF)) & 0xFFFF;
for (unsigned int EodCh = 0; EodCh < 2; EodCh++)
{
for (unsigned int TkHYN = 0; TkHYN < 3; TkHYN++)
{
ORZzX = ((ORZzX & 0xFFFF) + 1) & 0xFFFF;
ORZzX = (((ORZzX & 0xFFFF) << 


